
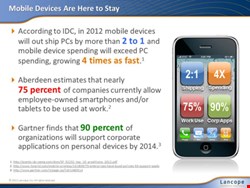

Beginning this year, mobile devices will exceed PCs in both shipments and spending. In the midst of increasingly sophisticated and trendy commercial devices, corporate users are taking mobility to new levels. They are expecting seamless access to company resources from any location and with any device, including their personal smartphones, tablets and laptops.
According to data from Aberdeen, 75% of companies currently allow employee-owned smartphones and/or tablets to be used at work. However, over half of all IT leaders in the US say that employee-owned mobile devices pose a greater risk to the enterprise than mobile devices supplied by the company.
The bring-your-own-device (BYOD) movement has significant productivity, convenience and cost benefits. Nevertheless, with so many unknown devices flooding the corporate environment, it is leading to serious challenges for IT administrators who are trying to come to terms with the fact that the network perimeter has vanished while the attack surface has increased.
The problem with BYOD is that most organizations have:
- Scarce knowledge of each device type, operating system, and patch level
- Limited control over policies governing which resources each device can and cannot access
- Incomplete information about who owns the device
- Lack of visibility into what the device is doing on the internal network and how confidential data is moving around
- Little understanding of the devices’ impact on the network
Administrators are struggling with the decision to either provide the business and employees with the resources they are asking for, or to provide a secure, locked-down environment. To balance out these risks with the business benefits of BYOD, organizations must adopt a more effective mobile security strategy.
To compound the problem, mobile users often circumvent corporate security policies and safeguards to gain convenient access to resources, and it is too cumbersome – and often impossible – to install and manage security software on every new device that enters the network. Unfortunately, traditional threat detection mechanisms such as anti-virus, IDS/IPS and other probe devices quickly become cost prohibitive, ineffective and unfeasible within a BYOD environment.
The only viable solution to the BYOD challenge is to obtain visibility into every single thing a mobile device is doing on the network. Without that, it is impossible to effectively ensure that the device is not accessing confidential, privileged data or carrying malware that could spread to other assets. The best way to regain this total visibility is to utilize the existing network. The network knows about every transaction crossing it, and it can provide this information in the form of flow data.
Already inherent in routers, switches and other network infrastructure devices, the use of flow data to monitor network and host activity provides a cost-effective solution for analyzing the behavior of mobile devices. With flow data, organizations can proactively detect issues stemming from any device on the network without having to install additional software on the devices or deploy expensive probes.
Flow-based monitoring can detect both externally launched, zero-day attacks such as botnets, worms or advanced persistent threats that bypass perimeter defenses, as well as internal risks such as network misuse, policy violations and data leakage. Advanced flow-based analysis solutions also trace issues to specific users and applications for greater contextual awareness, resulting in expedited incident response and more comprehensive forensic investigations. Other advanced features, such as automatic threat prioritization and mitigation, further streamline troubleshooting, eliminating the need for manual analysis and saving organizations vast amounts of time and resources.
Now is the time for enterprises to re-evaluate and strengthen their mobile security strategies to fit constantly expanding network infrastructure and user needs. While conventional defenses are losing their efficacy amidst a rapidly evolving technology environment, next-generation solutions are emerging that leverage existing infrastructure to deliver seamless security monitoring for any device that enters the network. These new solutions are enabling organizations to reclaim the situational awareness they need to maintain high levels of security in light of IT consumerization and BYOD.
Lancope, Inc is exhibiting at Infosecurity Europe 2012, the No. 1 industry event in Europe held on 24–26 April 2012 at Earl’s Court, London. The event provides an unrivalled free education program, exhibitors showcasing new and emerging technologies, and offers practical and professional expertise. Visit the Infosecurity Europe website for further information. |
Joe Yeager is director of product management at Lancope, responsible for the innovation and advancement of the company’s six StealthWatch product lines. Prior to Lancope, Yeager was a product manager for Hewlett-Packard in its Application Security Center division, where he oversaw WebInspect, an industry-leading web application security solution. At Hewlett-Packard, Yeager successfully brought large-scale product releases to a market of over 1,300 customers worldwide. Earlier in his career, Yeager was in charge of pre- and post-sales support for all international customers of SPI Dynamics, based in its London office. Yeager holds a BS in computer science from the Georgia Institute of Technology.