Earlier this year, a whitepaper was released which revealed the results of an experiment where malicious USB sticks were dropped around the campus of the University of Illinois. Working with researcher Elie Bursztein, the test gained further exposure this week at the Black Hat Conference in Las Vegas, with Bursztein declaring that they had been able to drop the USBs and it was “job done”.
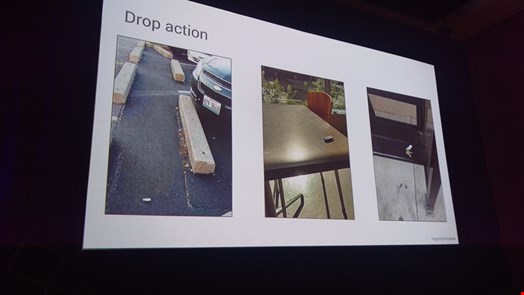
Going into great detail on the building of the USB sticks, the social engineering tactics to make it work and selecting the methods of attack, Bursztein demonstrated how simple it was to drop USB sticks outside, in the hallway, classroom, parking lot and academic rooms, and of the 297 sticks dropped, 290 were picked up and 135 (45%) called home.
Bursztein explained to the audience that they wanted those that picked them up to actually plug them in, and explain back why they did so, so one of the files contained a survey which was completed by 62 people. Also, 53 people offered to return the key.
In terms of the attack method used, Bursztein said that there were three options: social engineering which relied on hoping that the collector opening the key and its contents; HID spoofing which injects keystrokes which results in commands and connects back to attacker and gives control; or a zero-day which is more complex and can only be used once.
Social engineering was selected, although the University prevented the use of HTML5 as they were worried about harming computers.
In order to encourage people to pick them up, some keys had door keys attached, some said “confidential” and some said “final exam” and had file names. As a result, the most opened keys were those collected in the parking lot (53%), while 68% of collectors said that they had plugged it in and opened files to determine the owner. Also, 20% of keys were opened in the first hour, and 70% were opened within 35 hours.
Rather than using the tried and tested USB Rubber Ducky, which he said was not an option due to its limited scripting language, Bursztein opted to build his own USB sticks using a Teensy 32 development board and building his own key, which came to a cost of around $40.
He gave full details of building the USB stick, and said that “spoofing is not new, but it was a challenge to weaponize and create device, and find a way to figure out for Windows, OSX and Linux and the key has to figure out what to do.”
He concluded his talk with recommendations on how not to be caught out, mainly to do some awareness training, to be mindful of what you plug into your computer, and as a final resort, blocking USB ports or using the kill switch USBkill to restrict the device. Yet he admitted that this is “not perfect”.
Bursztein opened his session with an image from the TV show Mr Robot, in which a dropped USB stick was deliberately used as a weaponized tactic. What was very clear was that the tactics to deploy such an effort do require incredible amounts of precision and detail, and this is a tactic that can be used effectively.
However this should also serve as a warning to businesses that the keys were so readily picked up and plugged in, and if security awareness teaches us anything, it is that this sort of action is to be dissuaded.