
Over the last few years, organizations of all sizes across various industries have grappled with the challenges posed by allowing staff to use personal technology at work. They have, however, also enjoyed the benefits of BYOD: more productive and flexible workforces, greater employee satisfaction, and even cost savings.
The BYOD challenge could also be called the ‘iPad problem’. Since Apple launched its iPad, sales of tablet devices have grown rapidly.
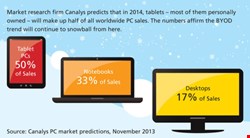
Canalys, a market research firm, suggests that this year (2014), tablets will account for almost 50% of all client PC devices, edging out conventional laptop computers as the portable device of choice. But, unlike the laptop PC, tablets are largely personally owned devices, over which businesses may have only limited control.
Canalys also believes Android will be the most common tablet operating system, and will run on 32% of client devices. Android is the most open of client device operating systems, and compared to Apple's iOS or Microsoft Windows, more open to malware.
The ‘iPad problem’, though, is one that has so far largely been driven by personal purchases by executives and senior management of what can still be a relatively expensive device.
A growing number of businesses, however, are deploying tablets – mostly running iOS and Android – for task-based workers. These are often being issued to field-based jobs such as engineering, maintenance, sales, healthcare or market research, although some financial firms have successfully rolled out tablets for traders and financial advisers.
Such applications, though, are typically tightly controlled by the corporate IT department, and should pose relatively few security or privacy issues to companies that take care over their deployments. The challenge, more often, lies in knowledge workers or managers asking for access to corporate systems on personal devices.
The challenge posed by tablets pales when set against the potential threats from smartphones. According to Gartner, the IT analysts, smartphones accounted for 55% of all mobile phone sales in the third quarter of 2013. With such momentum behind the smartphone, it is inevitable that employees will own them – and in turn, want to use them at work.
“The person bringing in a smart device expects to be able to use that for personal and corporate tasks”, says Bret Hartman, CTO for security at Cisco, the networking company. “The risk really has to do with the mix of the data and use of the device, which wasn’t designed to manage that separation.”
In fact, modern personal devices start out with exactly the opposite design philosophy: they are made to make sharing information easy, whether that is a social media post or a photograph.
This is a phenomenon that Nicko van Someren, CTO at mobile management vendor Good Technology, describes as “leakiness by design.”
“Consumer-focused design decisions are not wrong”, he adds, “but you need enterprise-grade protection. You have to make sure enterprise data doesn’t leak into the personal world – that they're not replicated to a home computer or a personal iPad, or synched to Dropbox or iCloud.”
Bring Your Own Problem?
“Companies are increasingly developing BYOD policies in the face of employee and executive pressure”, says David Dalva, a vice president at Stroz Friedberg, the risk management firm. “We often see a tension between device flexibility desires and the need to secure mobile devices. The outcome comes down to a business decision about the level of risk the leadership is willing to tolerate.”
Unless applications and devices are locked down to prevent it, it is all too easy for well-meaning employees to download documents and then sync that content to a consumer cloud service or device: often this happens in the background, and the device owner might not even know it has taken place. That is no defense for a company if that data subsequently leaks, or is stolen.
A further challenge is posed by the way we have a very personal relationship with our devices. According to Stephane Vinsot, at mobile identity and security vendor Gemalto, that relationship is so close that often, we struggle to see a device such as a smartphone as posing a threat.
Yet very, very few smartphone owners install anti-malware applications, firewalls or encryption, even when many of those applications are available at no cost.
This personal relationship also affects the way we use functions in smartphones and tablets, such as messaging, voicemail, memo recording or the camera. Even GPS captures location information that companies might not want disclosed.
Above all, a smartphone camera can be a powerful way of harvesting confidential information, should it fall into the wrong hands. “Information in photos on a personal phone can be quite sensitive”, says Morten Schultz, an expert in ICT-enabled business change at PA Consulting Group, the management consultants.
As the memory and the resolution of these cameras improve, they will only become more powerful, yet it is a feature that companies may well forget to lock down. If the phone is a personal device, there may be little companies can do to prevent its use, other than user education or, possibly, for the most sensitive areas and job roles, an outright ban.
A Mature Approach?
Organizations are, however, starting to take a more formalized approach to BYOD. While CIOs and IT security teams might not all be enthusiasts for BYOD, there has certainly been a shift away from opposing the use of personal devices.
“For most businesses, BYOD is pretty mainstream”, says Good's van Someren. “It has gone from the IT organization railing against the idea of people bringing their own devices, through grudging acceptance, to a model of embracing it.” This means putting in place both technical and policy measures to control the main risks.
Technical measures, such as mobile device management (MDM) and data-loss prevention tools can lock down or secure mobile devices. Increasingly, these tools are cross platform, and can manage laptops as well as smartphones and tablets. “Adequate security is possible now. It's getting easier”, says Tim Patrick-Smith, CIO at consulting firm Getronics.
Such tools, though, require employees to cede at least some control over their personal device to their employer, and may require them to download software to create an ‘enterprise’ partition on the personal device. Otherwise, standard MDM tools – such as remote lock and wipe – will destroy personal data alongside business data. This is rarely desirable, and in some countries, it is not permissible.
“If you have personal device, it's not the enterprise's right to wipe that device, and wipe personal music or photos”, van Someren comments.
Despite this, systems designed to implant separate work and personal ‘personalities’ into smart devices have met with limited market success. BlackBerry offers its Balance technology, and dual personal and enterprise partitions were a feature of Nokia enterprise devices running Symbian. But it is not a native feature in iOS or Android, and so not something employees will have automatic access to.
| "Unfortunately, BYOD is often treated as a technological problem with IT professionals dominating the discussion. But governance and compliance are essential aspects" |
| Jamal Elmellas, Auriga |
Some businesses are working around the issue by using virtualization to create a separate, secure sandbox for enterprise applications and data. Others are using specialist tools for enterprise communications, but this can give rise to duplication of key resources, such as inboxes and calendars.
As a result, some experts feel that a policy-based approach, perhaps in tandem with tools such as MDM, is preferable to relying on technology alone.
“Unfortunately, BYOD is often treated as a technological problem with IT professionals dominating the discussion. But governance and compliance are essential aspects”, says Jamal Elmellas, technical director of Auriga, an IT and security consultancy.
“You really need to understand the business and day-to-day processes before you can find a technological fit”, he adds. “You can then address other concerns, such as geographical location, connectivity, and intentions. The majority of products out there are offering ‘assured separation', allowing users to use their own equipment and separate critical business assets from private use. But how far should you go with separation?”
Not in My Sandbox
Options range from simply sandboxing files, to technologies that wipe all corporate information as soon as a device goes off site. But these systems may be overkill for the majority of businesses.
On the other hand, network-based solutions, such as data loss prevention and network-based traffic monitoring, offer a way of controlling where the data goes, but only if the personal device is connected to a corporate (wireless) LAN.
They are less effective when users are running devices over commercial cellular networks, as the business' security tools cannot see inside the cellular network, although controls can detect when sensitive data leaves the corporate network.
Despite these limitations, some degree of control is always necessary, as part of a BYOD strategy, if only to safeguard the organization against loss or theft of a personal device.
But security experts are increasingly worried about the threat to mobile devices themselves. Aside from the risk posed by lost or stolen devices, and of accidental data leakage, there are threats posed by apps, as well as mobile malware.
“The apps users download are increasing exponentially, and many are known to be buggy, if not downright dangerous”, warns Fran Howarth, principal analyst at Bloor Research. “In terms of the malware risks, these are becoming increasingly real, since attackers are focusing to a much greater extent on mobile malware, even if it is not yet at the level of malware attacking computers.”
Set against this threat, though, is the possibility that a well-designed BYOD policy can actually reduce risks and reduce the threat. “A well-defined BYOD policy will decrease the attack surface, certainly compared with not doing anything”, suggests PA Consulting's Schultz.
And there can be a further benefit, as measures to protect personal mobile devices extend to company-owned devices too.
“Putting in these systems also allows you to relax controls over the company's own devices”, says Getronics' Tim Patrick-Smith.
What is less clear, however, is whether BYOD saves companies money. “BYOD saves companies on hardware costs because employees buy them themselves. However, the company still has to pay for processes and technology to secure these devices no matter who buys them”, says Stroz Friedberg's Dalva.
It can save capital expenditure on devices in the short term, but unless employees are given a fixed allowance or stipend, the costs are often expensed back. And, as Bloor's Howarth points out, companies repaying personal cellular charges are unlikely to benefit from enterprise bulk discounts.
Nor is it possible for most organizations to move entirely to BYOD. The result is the need to manage two fleets of devices, personal and corporate, with the complexity and costs that entails.
“It will probably be a while before employers can get away with not providing the tools people need to do their job”, says PA's Morten Schultz. “We have worked with several clients who embark on a BYOD project only to realize that what is really needed is revised strategy for corporate devices and mobility.”
For BYOD to succeed, organizations need to understand who is using which device, where, and above all, why.