Phil Muncaster discovers that a combination of surging crypto prices and the pandemic have given cyber-criminals a shot in the arm...
There was a time a few years ago when cryptojacking supplanted ransomware as the pre-eminent global cyber-threat. As detections of the latter slumped in 2018, incidents involving cryptocurrency mining malware surged on the back of a thriving digital currency market. Many commentators claimed this was a sign of things to come. Cryptojacking is easier to make money from because threat actors don’t need to extract payment directly from their victims – they simply add more compromised machines to ramp up mining capability. Or so the argument went.
Then came ransomware-as-a-service, affiliate groups and double extortion – driving a renaissance in ransomware that saw attacks soar 485% in 2020, as home workers and remote access infrastructure were remorselessly targeted during the pandemic. Yet cryptojacking never went away. In fact, it evolved in the intervening years to become something arguably even more prolific. So the question is, should CISOs really care if the only apparent impacts are higher energy bills and slightly slower servers?
Stealing Compute Power
Cryptojacking, on the face of it, has always seemed a lower-level threat than the likes of data breaches, banking Trojans, DDoS and of course, ransomware. At a very high level, it involves the unauthorized use of a victim’s computing power to mine for cryptocurrency in order to generate profits. A variety of coin mining malware has been designed to achieve these ends. Enterprise targets offer arguably the richest pickings in terms of processing and memory resources, although campaigns have been known to go for large numbers of lower-powered smart devices conscripted into coin mining botnets.
One thing is clear: it’s still a popular way to make money. CrowdStrike’s recent OverWatch report recorded a 100% year-on-year increase in detections of cryptojacking intrusions, which it puts down to a sharp rise in the value of digital currencies from late 2020. Skybox Security claims to have seen double the volume of cryptojacking malware in the first half of 2021 versus the previous year. Monero remains the most popular currency to target, as the mining requirements are much lower than those for Bitcoin and there’s no tracking of transactions.
What’s Changed Since 2018?
To an extent, the same techniques are being used to get coin-mining code onto victim systems today as they were when Infosecurity reported on cryptojacking three years ago. That means scripts embedded into web pages that automatically execute when users visit, or phishing tactics designed to trick users into installing the malware directly on their machines.
However, some actors are going to more extraordinary lengths to stay hidden, according to Nathaniel Quist, senior threat researcher at Palo Alto Networks’ Unit 42.
“Cryptojacking groups vary in sophistication and capability. Some groups, like those behind campaigns such as dbused, avalonsaber and opsec_x12 appear to use copied, stolen or patched-together code, which lends their operations to being easier to detect and prevent. Others such as TeamTNT, Lemon_Duck and WatchDog have elevated their cryptojacking operations to include near zero day, or 1-day, attacks against cloud infrastructure,” he explains to Infosecurity.
“Cryptojacking groups vary in sophistication and capability"
“Lemon Duck has begun targeting cloud Microsoft Server instances that are vulnerable to ProxyLogon. WatchDog has included 32 unique remote code execution exploits within its cryptojacking malware, and TeamTNT has developed some of the first Kubernetes lateral movement attacks designed specifically to increase their mining operations. Each of these groups is considered to be technically proficient and a persistent threat.”
The pandemic has also unintentionally benefited cryptojackers. Although remote and hybrid workers aren’t being targeted directly, as enterprise resources offer more bang for the buck, the growing public cloud infrastructure needed to support them is targeted directly.
“The growing use of public cloud infrastructure as more users work remotely not only expands the attack surface of devices, but it also increases the management complexity and risk from shared cloud services,” CrowdStrike threat expert Scott Taschler tells Infosecurity.
“They’re facing new kinds of cyber-attacks. They’re accessing data and apps in the cloud, often from personal devices. They may not be protected by the security controls you’ve deployed across your network. Adversaries are looking to take advantage of any human error and misconfigurations from devices, and all lapses in IT hygiene increase the risk that a determined attacker will find a way to gain access.”
Unit 42’s Quist agrees that cloud environments have been the subject of mounting cryptojacking activity in recent months.
“We saw a rise in security incidents across nearly all industry verticals with retail, manufacturing and government leading the rest. This is significant as these three industries also saw the largest increase in the creation of cloud workloads during the same time, April to June 2021,” he argues.
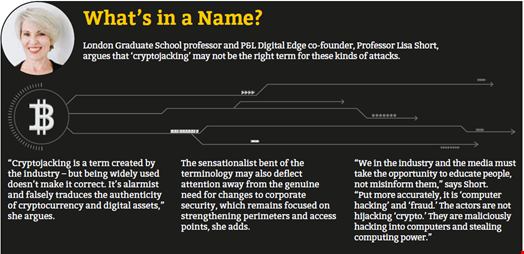
Lisa Short, a professor at London Graduate School and co-founder of P&L Digital Edge, argues that SMEs may be particularly at risk today.
“Widespread use of third-party JavaScript is making it easier for cyber-criminals to infiltrate websites with client-side attacks. They are particularly effective at exploiting non-technical SME websites, often self-built with low security and snippets of code copy-and-pasted into editing software,” she tells Infosecurity.
“Obviously, the move to remote working and vertiginous rise in digital transformation by the 99% of the economy which are small businesses, has exposed a new vulnerability for exploitation by these hackers and cyber-criminals.”
Hitting Back and Shifting Left
Security experts have long sought to raise awareness about the potentially severe repercussions of a cryptojacking infection. Yes, the bad guys are ultimately ‘only’ stealing your compute power, and yes, there’s a relatively minimal regulatory risk from being compromised. However, there’s a genuine risk that an attacker may not stop there. With possible access to your networked machines, what’s to prevent them monetizing one step further by deploying ransomware or info-stealing malware, for example? As such, organizations should get a handle on mitigation. The good news is that well-understood industry best practices will go a long way to diffusing the threat.
“Security teams must be able to identify an event and understand the attack vector, they must be able to stop an active breach and remediate systems quickly and they must learn from an attack and close security gaps"
“Security teams must be able to identify an event and understand the attack vector, they must be able to stop an active breach and remediate systems quickly and they must learn from an attack and close security gaps,” says CrowdStrike’s Taschler.
“As ever, organizations must always practice strong security hygiene: regularly patching vulnerable apps and operating systems, and protecting privileged user accounts. They need an endpoint protection platform so that they are able to prevent and detect all threats, including known and unknown malware, as well as identifying in-memory attacks.”
For Unit 42’s Quist, cloud-based next-gen firewalls are a great place to start to help detect malicious network traffic and malware targeting cloud environments. Nevertheless, organizations should also adopt and enforce industry standards such as CIS benchmarks, and more fundamentally, adopt a ‘shift-left’ security mindset, he adds.
“Embed cloud security directly into your code reviews and development pipeline by scanning for vulnerabilities and misconfigurations,” Quist argues. “The earlier development teams can find and remove security risks from their cloud architecture, the more secure the final production architecture will be.”
For Short, the very nature of cryptocurrencies may aid the work of investigators.
“We don’t talk enough about transparency and the evidentiary asset trails that blockchain affords to protect business assets rather than just to store and transfer value,” she concludes. “Bear in mind that all digital assets, not just crypto, have an evidentiary trail on a blockchain, so capturing the criminals and recovering assets is much easier.”