The discovery of the Spectre ‘mega-vulnerability’ was right up there with WannaCry in terms of cybersecurity industry response and mainstream media coverage, if not actual immediate damage. Davey Winder delves into the truth behind Spectre, the fundamental issues it brings to light and its potential impact going forward
Spectre was two of a trio of processor vulnerabilities, the third being Meltdown, that hit the headlines after being disclosed by Jann Horn, part of the Project Zero team at Google, on January 3 2018. Before that disclosure, several other security researchers had also reported the flaws. AMD, ARM and Intel were all informed in June, and had been working on mitigations in both hardware and software since then.
Meltdown (CVE-2017-5754) is so called as it effectively ‘melts’ the mechanism to prevent unprivileged user processes from reading kernel and physical memory. The vulnerability within the CPU ‘out of order execution’ process enables an attacker to use a side-channel exploit that reads the kernel memory value. As code running user-space privileges is not allowed to do this directly, an exception is raised, which is good.
The vulnerable CPUs also contain a ‘race condition’ (where output is dependent on the sequence of other uncontrollable events), which is bad. This enables any ‘out-of-order’ instructions to execute before the exception is raised, and the cache-state doesn’t revert when the CPU rolls back the instructions. This means that the attacker could access the memory of virtual machines hosted within the same cloud system, thus potentially leading to privilege escalation exploits of those machines. OS vendors and cloud providers can mitigate Meltdown with patches, but as the out-of-order mechanism is a performance enhancing one, these can negatively impact upon processing speed.
Spectre (CVE-2017-5715 and CVE-2017-5753), so-called as it involves speculative execution within the CPU’s branch prediction capabilities, can also be exploited using side-channel attacks to trick applications into accessing arbitrary memory locations. Branch prediction is a feature that enables a processor that reaches a conditional branch without having already been told what to do, to speculate and execute based upon past decisions made. This improves performance by minimizing waiting time and utilizing more parts of the CPU itself.
Unfortunately, while the speculative instructions are discarded in both a successful and unsuccessful prediction, in the latter, any indirect effects (such as changes in the CPU cache) are not. This provides an attacker with the potential to measure memory access operation latency, and extract values from the speculative instructions. The technicalities differ between the two CVEs in that CVE-2017-5753 speculatively executes instructions after a conditional branch as the result of misprediction, while with CVE-2017-5715 the instructions are executed at the location determined by the ‘mispredicted’ target. In other words, it can extract ‘secret’ data such as passwords stored in a browser client from a target process. It’s agreed that Spectre is a harder exploit to effect, but also to mitigate as those exploits will mainly be custom-made to match specific processes. It’s vendor-agnostic as well, and has a much broader reach.
“It’s likely that many attackers have already tried taking advantage of such vulnerabilities"
Looking Ahead
The potential impact from Spectre could continue for years to come. Data leaks via cache side-channel vulnerabilities are going to be a concern for processor engineers for several years, thinks Caleb Fenton, threat team lead at SentinelOne, since their product cycles take several years.
“Security researchers are like sharks, and there’s blood in the water,” he tells Infosecurity. “I’d expect to see new, related vulnerabilities discovered in the coming years since so many researchers are looking at this now.” Given that pretty much anything accessible to the browser could theoretically be accessed using Spectre, the biggest challenge could come if these vulnerabilities were worked into exploit kits. “While the sheer volume of data that could be captured makes it more difficult for attackers to find valuable data that could be used against individuals at scale, they could be used as part of targeted attacks,” says Jimmy Graham, director of product management at Qualys.
Of course, right now nobody is sure of anything as the complete range of potential exploits through Spectre are not yet properly understood, and most attack scenarios remain theoretical.
“I guarantee, however, once a determined cyber-criminal finds a way to monetize the exploits or a Nation State finds a way to use the vulnerability for other means, we’ll start to understand the full fallout,” concludes David Dufour, senior director of cybersecurity and engineering at Webroot.
The Business Issues
So, what are the fundamental business security issues that Spectre has exposed? Many industry experts agree that the biggest threat from Spectre sits in cloud provision territory. According to Chris Morales, head of security analytics at Vectra, there is an ongoing debate as to the real effectiveness of the Intel patches against various attack methods.
“It is likely these debates will continue,” he tells Infosecurity, “and further research by the security community will be conducted, to pinpoint both the cause and solution.” Indeed, while the larger cloud providers were informed of Spectre ahead of the public disclosure and able to patch, according to James Maude, lead security engineer at Avecto, “many smaller providers are still playing catch up, which is raising concerns about the security of the data on these platforms.”
That could, for any organization that works with secure data, lead to cloud-based solutions being decelerated in favor of a migration to dedicated bare-metal servers more within their control. “It’s likely that many attackers have already tried taking advantage of such vulnerabilities by spinning up free server instances on the likes of Amazon Web Services and Azure,” warns Ken Gilmour, CTO and co-founder of Invinsec.
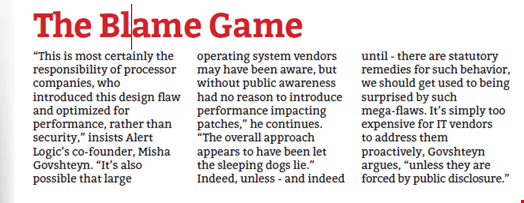
The truth is that we just don’t know, as the exploitation of Spectre is all but impossible to detect. We may never be able to confirm a breach directly to Spectre unless malicious exploit code appears in the wild, which is why Misha Govshteyn, SVP and co-founder of Alert Logic, says most of the public impact will be on the disruption these issues introduce, measured as the immense cost of pushing these patches across nearly all IT infrastructure.
“In some ways, this may end up feeling like Y2K,” he explains, “with endless resources spent on fixing the problem, but little noticeable impact we can clearly point to.” Apart from the impact on performance hits that patching the vulnerability introduces, that is. “If your architecture has become 5% less efficient then you have to buy 5% more equipment to get back to where you were before this happened,” warns Ross Rustici, senior director of intelligence services at Cybereason, who concludes that Spectre is one of the few times where avoiding a cyber-incident is likely to have a quantifiable, unplanned impact on the bottom line of many businesses.