This past Saturday I attended a capture the flag (CTF) tournament with a twist on the information security skills shortage.
You could argue that most efforts like CTF are about enhancing skills, allowing teams to work together in a ‘gamification’ format and focus on building and enhancing attack and defense skills. This particular event was held by Inter-ACE at Cambridge University’s computer science lab, the second annual event with teams participating from UK universities.
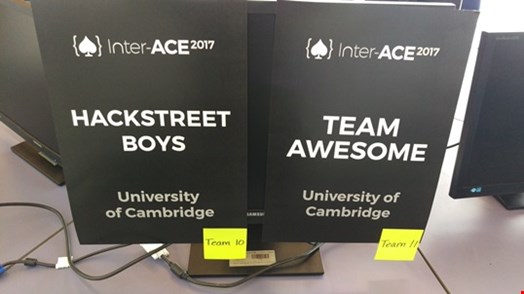
In total, around 100 participants fitted into 26 teams from 11 universities: the University of Birmingham; University of Cambridge; Imperial College; Queens University Belfast; University of Oxford; UCL; Lancaster University; University of Southampton; Royal Holloway; University of Kent and the University of Surrey. Sponsored by Leidos and NCC Group and supported by the National Cyber Security Centre and Cabinet Office, the teams battled for a share of the £10,000 prize which would be divided among the first, second and third placed teams.
Opening the event, Dr Frank Stajano, reader in security and privacy at the University of Cambridge and founder of Inter-Ace, related to the Cyber UK conference from earlier in the week, saying that the mandate of the National Cyber Security Centre is to establish the UK as the “safest place to do business online” and for that, the country needs “infosec talent in the private and public sector, boardroom and classroom.”

The competition itself went on for five hours, where live scoreboards were removed for the final hour and revealed later in the evening. The concept was that the teams were information security professionals working for a fictional power company called ‘Transcorp’ which had been taken over, and it was the job of the teams to use their skills to take back the network, secure and remove the attackers and find out the source of the leaks.
Speaking to Infosecurity, Stajano said that the intention of the exercise was to build up a network of ‘smart individuals’ to prepare students for work.
“These universities are recognized as centers of excellence in cybersecurity, and bringing the students in to do something practical with cyber-skills,” he said. “As the academic centers are about research, working on cyber-skills will maybe attract them to the industry and maybe recruit them into industry and help secure our nation.
“This is slightly different as young students find that it is interesting, challenging and potentially lucrative, and they will be in great demand so it is a good career move. At the same time we want to put the smart people in touch so they can create a network now to rely on once they are in a position of responsibility as nowadays they are students, but once they are graduates with responsibility for a company or a whole country then they have in their address book people that they made friends with back in 2017.”
One question levied at CTF challenges is that there is too much focus upon offensive skills, and I asked Stajano if he felt that the students were getting a rounded bunch of skills in this environment. He said that Inter-ACE cares about people who can protect from the bad guys, “and I like to think we are not the bad guys!”
“To only defend is essentially impossible, so you are not going to be skilled at defense unless you know how many times you are going to be broken,” he said.
If you are able to pick the locks now and know where the weaknesses are, just doing defense you are not going to be very good at it so you need to have the same level between attack and defense be good at security as a whole.
“The objective is to use that skill at defending the assets of people. We are not training people to go and attack other places, but we need them to be skilled at attack as otherwise they are not going to be up for the challenge if the attacker comes from outside.”
I later took the opportunity to talk to some of the participants. Tom, a third year undergraduate studying electronics at the University of Southampton, whose team were in second place at the time of talking to Infosecurity, and would later claim second prize overall and £2500 for the team, said that the event was pretty good, and his team had "only messed around with simple things but it seems to be working".
Asked if this had turned him on to the area of cybersecurity as a career option, he said: “I chose it as a module and I don’t know what I will do next, I was going to do more electronics but I may change to cryptography as another choice.”
Marie-Sarah, a second year PhD student of information security and cryptography from Royal Holloway University, said that she had just joined the CTF team six months ago, but she had participated in individual events in the past but not in an event such as this.
She said she had mostly spent the day on the forensics investigation side of the challenge, and the whole event had been going well. Looking to the future, she told Infosecurity that she planned an internship for later in the year, to help her decide if she wanted to stay in academia or work.

Later in the evening, at a dinner held in the Great Hall of Trinity College, the winning team was named as team QWERTY from Imperial College London, who were awarded £6500, with the team now guaranteed a place in the annual Cambridge2Cambridge (C2C) cyber competition later in the summer, which is jointly organized by the University of Cambridge and the Massachusetts Institute of Technology (MIT) Boston.
From the winning team, Luke Granger-Brown, who is studying computing at Imperial College London, said: “It has been an incredible competition, and I’m surprised we won. We would encourage everyone to participate who can in the next competition, as it’s a great way to put the stuff we have learnt at university into practice.”
That was Inter-ACE 2017, a new initiative to make students aware of the career opportunities that exist in cybersecurity, and a chance to compete directly against other university students who may be as skilled as they are. This is a positive thing and one I hope come 2018 it will be even larger as university computing departments realize the opportunity for learning.
