A cyber espionage group linked to North Korea has been observed deploying a new malicious campaign using removable media infection tools to gain access to air-gapped systems.
The group, APT37, is well-known hacking team active since at least 2012 and known under many names, including ScarCruft, Ruby Sleet, InkySquid, Ricochet Chollima and Velvet Chollima.
Initially focused on the public and private sectors in South Korea, the group expanded its operations in 2017 to include Japan, Vietnam and the Middle East, and to a wider range of industry verticals, including chemicals, electronics, manufacturing, aerospace, automotive and healthcare entities.
Read more: North Korean Hackers Weaponize Seoul Intelligence Files to Target South Koreans
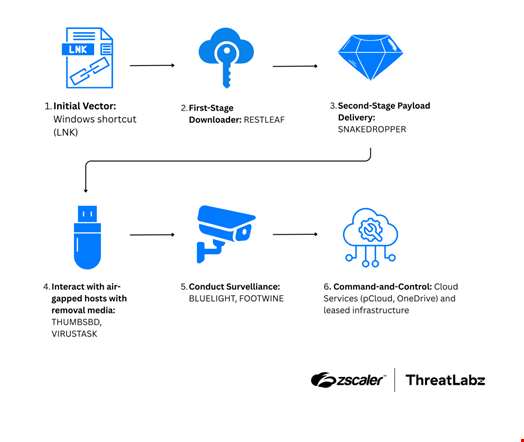
In this new campaign, spotted by security researchers at Zscaler ThreatLabz and dubbed ‘Ruby Jumper,’ APT37 utilized a set of six malicious tools throughout the attack lifecycle, five of which had never been documented (Restleaf, SnakeDropper, ThumbSBD, VirusTask and FootWine).
It also leveraged removable media to infect and pass commands and information between air-gapped systems.
APT37’s Ruby Jumper Campaign Explained
The Ruby Jumper campaign was discovered by the ThreatLabz team in December 2025.
During this campaign, documented in a report published on February 26, APT37 gained access using the group’s traditional method: abusing Windows shortcut (LNK) files.
When a victim opens a malicious LNK file, it launches a PowerShell command and scans the current directory to locate itself based on file size. Then, the PowerShell script launched by the LNK file carves multiple embedded payloads from fixed offsets within that LNK, including a decoy document, an executable payload, an additional PowerShell script and a batch file.
This document displays an article about the Palestine-Israel conflict, translated from a North Korean newspaper into Arabic.
The executable payload is a newly discovered implant, dubbed Restleaf by the ThreatLabz team, that uses Zoho WorkDrive for command-and-control (C2) communications to fetch additional payloads.
“To our knowledge, this is the first time APT37 has abused Zoho WorkDrive,” the researchers noted.
RestLeaf profiles the compromised system and establishes persistence before retrieving follow‑on components from Zoho WorkDrive. Among these is SnakeDropper, a loader responsible for decrypting and deploying additional modules in memory, reducing on‑disk artefacts.
To extend access beyond the initially infected host, APT37 deploys ThumbSBD, a tool specifically designed to propagate via removable media.
ThumbSBD monitors for connected USB drives, copies a tailored infection package onto them and abuses shortcut files to ensure execution when the drive is opened on another system. This enables lateral movement into isolated or segmented environments.
When a USB device reaches an air‑gapped machine, the infection chain resumes.
VirusTask executes as a lightweight backdoor, collecting system information and staging data for exfiltration. Because the system lacks direct internet access, APT37 again relies on removable media: stolen data is written back to the USB drive in hidden or obfuscated form.
The operators also deploy FootWine, a reconnaissance and collection utility focused on harvesting documents and monitoring removable drive activity, ensuring valuable data is queued for extraction.
Supporting these newer components is BlueLight, a previously documented APT37 tool used for command execution and data theft. In connected environments, BlueLight communicates with external C2 infrastructure. In air‑gapped scenarios, it facilitates tasking and data staging for delayed exfiltration via USB.