Over two-thirds (69%) of organizations experienced a successful ransomware incident in the past year, according to Proofpoint’s 2024 State of the Phish report.
This represents a rise of five percentage points compared to the previous year, according to the firm.
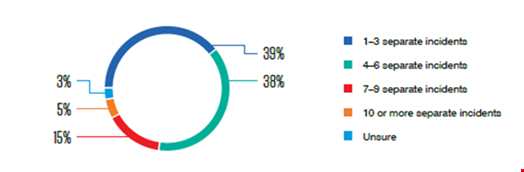
Close to 60% of these organizations reported four or more separate ransomware incidents in 2023, emphasizing the scale of this threat.
Over half (54%) of infected organizations admitted they paid a ransom to attackers. This marks a significant reduction on the proportion who paid in the previous year, which was 64%.
Paying a ransom was no guarantee of resolving the issue, with just 41% of organizations who paid regaining access to data after their first payment.
On February 23, 2024, Cybereason published research showing that 78% of organizations who paid a ransom demand were hit by a second ransomware attack, often by the same threat actor.
Almost all (96%) of organizations impacted by ransomware no have cyber insurance. More than nine in 10 (91%) of insurers helped with ransom payments in 2023, up from 82% in 2022.
Read here: LockBit Takedown: What You Need to Know about Operation Cronos
MFA Bypass and Other Social Engineering Trends
The Proofpoint research highlighted that attackers are increasingly using advanced techniques to bypass multifactor authentication (MFA). Typically, these techniques involve proxy servers to intercept MFA tokens, with several off-the-shelf phishing kits now including MFA bypass functionality.
For example, the company said it observes around one million phishing threats use the EvilProxy framework every month. This tool is based on a reverse proxy architecture which is designed to harvest MFA-protected credentials and session cookies.
Despite the growing availability of MFA bypass capabilities, 89% of cybersecurity professionals surveyed still consider MFA to provide complete protection against account takeover.
Attackers are evolving their social engineering techniques in a range of other ways. This includes an increase in the use of QR codes as an alternative to links or attachments in phishing messages.
The researchers noted that this technique is particularly dangerous as it is more likely to evade automated detection and it is impossible for recipients to tell just by looking if a QR code leads to a phishing site or malware download.
Another prominent threat was business email compromise (BEC) attacks, with 73% of organizations targeted. Proofpoint’s own data also showed an average of 66 million targeted BEC attacks globally each month.
There was a particular surge in BEC attacks targeting countries such as Japan (35% rise), South Korea (31%) and UAE (29%) compared to the previous years. The researchers believe this increase is linked to generative AI, which is enabling attackers to create more convincing and personalized emails in multiple languages.
The brand most commonly impersonated for phishing and malware delivery was Microsoft, with more than 68 million messages associated with the tech giant’s products and brand in 2023. This was followed by Adobe (9.4 million) and DHL (8.8 million).
Risky Security Behavior Prevalent
More than two-thirds (71%) of working adults included in the survey admitted taking a risky action. These included using work devices for personal activities (29%), reusing or sharing a password (26%), and connecting without using VPN at a public place (26%).
Of those who took risky behaviors, 96% acknowledged they did so knowingly.
The primary reasons for taking risky actions were convenience (44%), to save time (39%) and to meet an urgent deadline (24%).
Ryan Kalember, chief strategy officer, Proofpoint, commented: “Cybercriminals know that humans can be easily exploited, either through negligence, compromised identity or – in some instances –malicious intent.”
He added: “While fostering security culture is important, training alone is not a silver bullet. Knowing what to do and doing it are two different things. The challenge is now not just awareness, but behavior change.”
