Russian nation-state group Sandworm is believed to be utilizing a novel backdoor to target organizations in Ukraine and other Eastern and Central European countries, according to WithSecure researchers.
The previously unreported backdoor, dubbed ‘Kapeka’, has a high level of stealth and sophistication, designed to both serve as an early-stage toolkit for its operators, and also to provide long-term access to the victim estate.
“Kapeka’s development and deployment likely follows the ongoing Russia-Ukraine conflict, with Kapeka being likely used in targeted attacks across Central and Eastern Europe ever since the illegal invasion of Ukraine in 2022,” the researchers wrote.
For example, they said the novel backdoor was likely used in intrusions that led to the deployment of Prestige ransomware in late 2022, which targeted transportation and logistics industries in Ukraine and Poland.
The technical analysis of Kapeka is designed to raise awareness amongst businesses, governments and the broader security community of the threat it poses.
Sandworm Using Novel Backdoor to Support Espionage Campaigns
In findings corroborated with Microsoft, WithSecure believes Kapeka is being used as a bespoke tool by Sandworm as part of wider espionage campaigns to support intelligence collection for the Russian state.
These campaigns can also lead to sabotage operations at later stages, including ransomware attacks, according to the report.
The Sandworm group is operated by Russia's military intelligence service, the GRU, and is known to support the wider strategic objectives and changing intelligence requirements of the Russian state.
The advanced persistent actor (APT) has been blamed for several destructive attacks against critical infrastructure organizations in Ukraine, including causing a power outage in 2022.
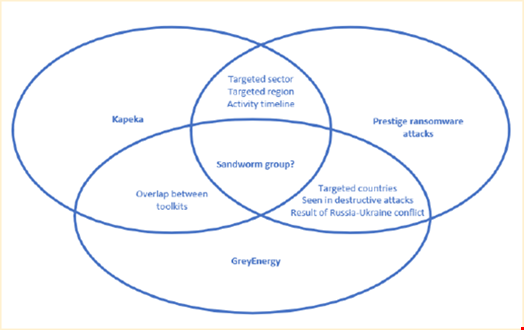
WithSecure cited several reasons why it assesses Kapeka is being used by Sandworm. These are:
- Numerous overlaps between Kapeka and GreyEnergy, a modular backdoor thought to be part of Sandworm’s arsenal. Kapeka is likely a successor to GreyEnergy
- Its infrequent sightings point to its meticulous usage by an APT in operations that span over years, such as the Russia-Ukraine conflict
- The level of stealth and sophistication also indicate advanced APT activity, highly likely of Russian origin
- Based on victimology, the backdoor was likely used in campaigns specifically targeting victims in Eastern Europe. It was first observed as part of an intrusion in an Estonian logistics company in late 2022, which was likely linked to Russian APT activity
However, the researchers acknowledged that they currently do not have sufficient data to state conclusively that it has become part of Sandworm’s arsenal.
How Kapeka is Used to Target Organizations
Kapeka contains a dropper that will drop and launch a backdoor on a victim’s machine and then remove itself.
The backdoor first collects information and fingerprints both the machine and user before sending the details on to the threat actor, allowing tasks to be passed back to the machine or the backdoor’s configuration to be updated.
It also contains a functionality to support the execution of custom payloads. This functionality essentially makes the backdoor modular by allowing additional modules to be dropped and executed.
As with GreyEnergy, Kapeka is a DLL file with a masqueraded extension to make it appear legitimate. Both backdoors use a similar custom algorithm to structure data that’s sent to their command and control (C2) infrastructure.
There are also several differences between Kapeka and GreyEnergy. For example, GreyEnergy utilizes WMI to fingerprint the victim, while Kapeka utilizes Windows API and registry.
Additionally, Kapeka persists its C2 configuration via registry, while GreyEnergy does so via a file on-disk.
While Kapeka and its dopper contain capabilities to remove all traces of compromise, WithSecure identified several infection artifacts and developed several scripts to aid with analysis and detection.
The researchers said they will continue to monitor the use of Kapeka.
“It remains to be seen whether the developers and operators of Kapeka will evolve with newer versions of the tool or develop and use a new toolkit with threads of similarity to Kapeka (such as conceptual overlaps or code re-use) like those found between Kapeka and GreyEnergy,” they added.
