The White House’s goal of bolstering the cyber resilience of critical infrastructure is being threatened by US federal agencies’ lack of oversight of ransomware protections, according to a new Government Accountability Office (GAO) report.
The GAO noted that some agencies only assess the adoption of basic cybersecurity protections and general guidance in critical sectors like energy and healthcare, rather than federal guidelines on addressing ransomware specifically.
The report analyzed ransomware mitigation strategies in four critical infrastructure sectors – critical manufacturing, energy, healthcare and public health, and transportation.
Most federal agencies that lead and manage risk for four critical sectors have assessed or plan to assess risks associated with ransomware, according to the GAO.
However, the agencies have not fully gauged the use of leading cybersecurity practices or whether federal support has mitigated risks effectively in the sectors.
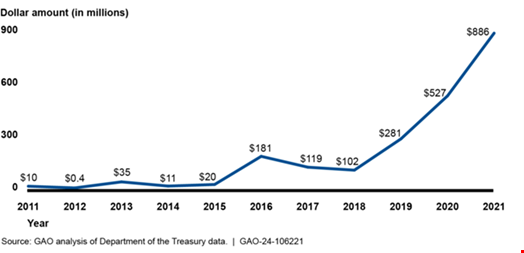
The findings come amid surging ransomware attacks in the past year, and prominent energy and water companies hit at the start of 2024.
Bolstering the cyber resilience of critical industries is a key aim of the White House’s National Cybersecurity Strategy, which was unveiled in 2023.
Lack of Assessment of Ransomware Protection Measures
NIST developed a cybersecurity framework for managing ransomware risk in February 2022. The framework aims help organizations identify and prioritize opportunities for improving their security and resilience against ransomware attacks.
However, none of the Sector Risk Management Agencies (SRMAs) the GAO assessed have determined the extent of adoption of the NIST ransomware profile as recommended by the National Infrastructure Protection Plan (NIPP), the GAO found.
“Until SRMAs understand sectors’ adoption of National Institute of Standards and Technology (NIST) or similar other practices that are intended to improve security and resilience against ransomware attacks, the White House’s goal of bolstering critical infrastructure resilience to withstand ransomware threats will be more difficult to achieve,” the GAO wrote.
The risk and management agencies did identify seven other sets of practices from federal agencies and the cybersecurity industry that were used to address ransomware.
However, the report noted that these practices focus on foundational cybersecurity protections to manage a variety of cyber threats beyond ransomware.
“Six of the seven sets of practices did not fully align to leading federal practices that NIST established to address ransomware,” wrote the GAO.
Many of the agencies and officials from the critical manufacturing, energy and transportation sectors said they were not familiar with NIST’s ransomware profile or did not identify it as one of the adopted sets of practices within the sector.
Improving Oversight of Ransomware Protection in Critical Infrastructure
The GAO made a total of 11 recommendations for the four SRMAs to improve the federal government’s oversight of the adoption of specific ransomware protections in the relevant critical infrastructure sectors.
These focused on the Secretaries of State developing and implementing routine evaluation procedures.
These are to measure the effectiveness of federal support in reducing the risk of ransomware to the sectors, and determine the extent to which they are adopting leading cybersecurity practices in this area.
The Department of Homeland Security (DHS) and Department of Health and Human Services (HHS) agreed with their recommendations.
The Department of Energy (DOE) partially agreed with one recommendation and disagreed with another.
The Department of transportation (DOT) agreed with one recommendation, partially agreed with one, and disagreed with a third.
Commenting, Mark B. Cooper, President & Founder, PKI Solutions, said the report revealed a worrying gap in the understanding and implementation of protections for core systems like identity and encryption in critical infrastructure.
“This situation also highlights the need for a more coordinated approach across agencies and a requirement for deeper level of assessment to Identity and Encryption systems. This is crucial for strengthening the operational resilience of critical infrastructure against ever changing cybersecurity threat landscape,” said Cooper.
