Earlier this year Lenovo got caught installing Superfish adware on its laptops. Superfish breaks open SSL/TLS encryption using forged digital certificates and unwittingly allows bad guys to exploit the digital trust they provide. Unfortunately, man-in-the-middle (MITM) attacks with forged certificates are nothing new.
The SSL/TLS trust model is designed to protect communications end-to-end. But Lenovo inserted the Superfish CA certificate as trusted, meaning that all of the MITM certificates were trusted within the browser, thereby exposing users to insecure sites or interception of private communications. Whilst Lenovo admitted its mistake and claims to no longer ship adware, it is clear that the system of trust established by keys and certificates is under attack.
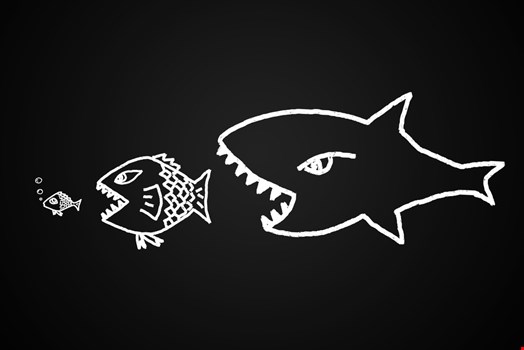
Keys and certificates were designed to be like the biological tags in living cells – identifying what’s safe and trusted. However, we left out one thing it seems: an immune system to keep up with what really is trusted. There’s a lot we can learn from our human immune system and apply to the cyber realm.
According to the Ponemon Institute’s 2015 Cost of Failed Trust report, as cyber-attacks grow, so do the number of keys and certificates. Over the past two years, the number of keys and certificates used on enterprise infrastructures such as web servers, network appliances and cloud services grew more than 34% to a staggering 24,000 per enterprise on average. Stolen certificates now sell for more than $1000 on the black market and have doubled in price in just 12 months. Yet, 54% of enterprises don’t actually know where all their keys and certificates are or how they are being used.
The gaps in security exposed by Superfish, Heartbleed, Poodle is a major concern and enterprises must look at their certificate-issuing supply chain to establish what certificates are being issued, and by whom, in order to shore up their security.
There are over 200 authorities issuing certificates, but it does not mean you can trust them. Earlier this year, Google and Mozilla announced that their browsers would no longer trust digital certificates issued by the China Internet Network Information Center (CNNIC), China’s main digital certificate authority. The decision came after Google said it discovered unauthorized certificates for a number of domains. Microsoft and Apple opted to take no action.
As an IT professional you should not simply follow the industry heavyweights, but do your own research and know which certificate authorities you are confident your enterprise should trust. As Gartner suggests, “Certificates can no longer be blindly trusted.”
If your company isn’t doing business with China, for example, why would you work with CNNIC? Reducing certificates installed on endpoints across the enterprise won’t eradicate all risks linked to the Certificate Authority system, but it does provide some clear steps to reducing exposure.
The Council of Cybersecurity’s Critical Security Controls provide a recommended set of actions for security defense that provide specific and actionable ways to prevent cyber-attacks. They look at what works in real-life scenarios in terms of security controls, products, architectures and services. The controls have been taken from common attack patterns and vetted across a broad range of government and industry organizations, thus providing the basis for a high-value defense action plan.
"Enterprises acknowledge a breach when it hits the headlines, but fail to understand how to respond and react"
The problem is that enterprises acknowledge a breach like Superfish when it hits the headlines, but fail to understand how to respond and react to the reality of the situation. This is the crux of the problem. IT security professionals must be proactive, look at Critical Security Controls updates, so that they can put stable defenses in place. These range from continual vulnerability assessment and remediation, an inventory of authorized and unauthorized software and devices, to data recovery capabilities and incident response and management.
As the Council of Security points out, there are endless lists of how to improve security in cyberspace, but there is no clarity on how to prioritize them. Its aim, as a community, is to provide answers to some of the most critical problems. For example, which defense steps have the greatest value? These are embraced in the Critical Security Controls updates.
During the last 12 months, significant vulnerabilities and breaches have shown how unsecured keys and certificates provide the trusted status cyber-criminals need to go undetected. It is clear that the very system of trust in the internet established by keys and certificates is under attack. Enterprises can no longer expect static defense mechanisms to protect them.
What we need is an immune system for the internet. Just as us humans have evolved a highly effective immune system, so we need to establish one for the internet that provides resistance to invasion, otherwise the internet will be at risk of sinking in a slurry of cyber-attacks.
