As COVID-19 vaccines finally become a reality, Phil Muncaster asks how cyber-threats and misinformation could disrupt their delivery
Experts have been warning for years that mankind’s increasing reliance on digital technologies could be its undoing. They claimed that targeted cyber-attacks will move beyond data monetization to threatening users with physical harm, while widespread misinformation and disinformation will destabilize societies and empower tyrants. With the arrival of COVID-19 and the urgent global effort to produce and distribute life-saving vaccines, these trends are rapidly transforming from theory into practice.
The UK government became the first in the West to begin roll-outs of the Pfizer/BioNTech vaccine in December, with the Oxford University/AstraZeneca and Moderna alternatives following shortly behind. From lab to jab, getting these to patients untainted and at the correct temperature will require the most ambitious supply chain operation ever conceived. Unfortunately, there are many moving parts, which means a large cyber-attack surface. There’s also a great deal of motivation for organized crime groups and nation states to steal, sabotage and spread fake news.
The Story So Far
Two alarm bells should be ringing from a cybersecurity perspective. The first is the pharmaceutical industry’s recent experience. According to a BlueVoyant report examining 20 of the world’s biggest pharma and biotech firms, including eight that are currently producing vaccines, 80% have suffered targeted attacks over the past year. Even worse, over a third (35%) showed signs of compromise. Furthermore, the report claimed that overall attacks surged 50% from 2019 to 2020.
The second major cause for concern is centered around the supply chain – which has been a security risk for companies for years. Although things are improving, smaller suppliers are often not held to the same high standards as their larger partners, so they become an attractive target for attackers looking to reach higher value data or networks. As the UK’s National Cyber Security Center (NCSC) warned in its 2018 guidance: “attackers have both the intent and ability to exploit vulnerabilities in supply chain security. This trend is real and growing. So, the need to act is clear.”
With COVID-19, the supply chain is more important than ever, especially in the case of the Pfizer vaccine, which needs to be transported at incredibly low temperatures in highly specialized containers. IBM has already spotted a global phishing campaign targeting these global cold chain providers, pointing the finger at nation state activity. State-backed hackers from China, Russia and North Korea were also in action over the course of 2020, targeting western vaccine makers and researchers multiple times in a likely bid to gain an advantage in developing a COVID-19 cure.
At the same time, organized crime groups could have both a direct and serious indirect impact on vaccination efforts. Europol has warned that such groups might seek to steal vaccines from suppliers in order to sell on to eager members of the public. The law enforcement organization also warned of fake vaccines being sold on the dark web. It claimed that if enough people fall for such scams, they may not turn up to appointments for the genuine vaccination, leading to further outbreaks.
An alternative scenario is, of course, that individuals refuse to take any vaccines, citing concerns over side-effects. Worryingly, just 42% of Americans said back in August they’d definitely take the vaccine when one is available. Conspiracy theories about vaccines have been circulating for years and research suggests that small Facebook groups have been prolific over recent months in spreading mistruth.
“Anything which interrupts the manufacturing and distribution process for vaccines, which delays production or undermines the quality of the product, will be high impact”
A Power Play
So what are the most likely cyber-threats facing vaccine supply chain companies over the coming months? According to former GCHQ director and chairman of BlueVoyant, Robert Hannigan, the “overwhelming majority” of activity will be financially-motivated cybercrime.
“Anything which interrupts the manufacturing and distribution process for vaccines, which delays production or undermines the quality of the product, will be high impact,” he tells Infosecurity. “The most likely cyber-attacks will be ransomware, especially targeted against industrial control systems. Criminal groups will know that manufacturers and transport companies are likely to pay to restore data and keep production running.”
However, experts haven’t ruled out more cyber-powered interference and disruption from nation states, beyond hunting for vaccine-related IP. That’s because there’s plenty at stake for hostile governments, according to Martyn Gill, former military and government intelligence expert and now global managing partner at Wembley Partners.
“The perception to be seen as the first to be vaccinating one’s own population is deemed to show strength. We can assess that Russia likes to take this line,” he tells Infosecurity. “Also, economically, to be able to get your country moving forward again, to gain a positive foothold on the global market, is definitely a driver and goal of nation states. Disruption of ‘rival’ states to accelerate this is not to be ruled out.”
There are multiple ways hostile states could disrupt rivals’ vaccination programs in this way, spoiling products in transit and even endangering patients, according to Shriram Ramanathan, director of research at Lux Research.
“In the case of vaccines, it is critical to ensure that temperatures, humidity and other factors are maintained within specific windows at all points in the supply chain in order to prevent spoilage,” he explains. “Cybersecurity vulnerabilities might lead to data tampering which, in turn, can pose a big risk to those who are vaccinated and can make it harder to pull a batch of spoiled products off the shelves quickly.”
Cyber-criminals could also benefit from data tampering by, for example, interfering in real-time tracking systems to steal supplies, or altering quality control diagnostics to replace products with counterfeits, he says.
Sowing Division
Misinformation about COVID-19 vaccines has also been growing online. Some of the more outlandish conspiracy theories are that the vaccine will be used to inject microchips into recipients or deliberately alter their DNA, which is technically impossible. Spreading such lies is straight out of the same nation state playbook that led to the hacking of Democratic Party officials before the 2016 US election. As Hannigan explains, the ultimate aim is to “sow division and polarize societies in the West.” By slowing uptake of the vaccine in rival nations, there’s also a theoretical opportunity for rogue states to pull ahead economically and geopolitically.
Gill adds that “political hacktivists” have also been at work here, spreading misinformation through social media. “In many cases, these actors are driven by their ideological and political beliefs. However, there remains a subset of actors who seek to cause disruption primarily as a means of entertainment,” he says.
Fortunately, it’s an issue the social media giants appear to be taking seriously. YouTube banned misinformation about vaccinations in October and Facebook followed suit in December last year.
“This is another way that we are applying our policy to remove misinformation about the virus that could lead to imminent physical harm. This could include false claims about the safety, efficacy, ingredients or side effects of the vaccines,” the social network said in a statement sent to Infosecurity. “We will also remove conspiracy theories about COVID-19 vaccines that we know today are false.”
“Cybersecurity vulnerabilities might lead to data tampering which, in turn, can pose a big risk to those who are vaccinated”
A United Front
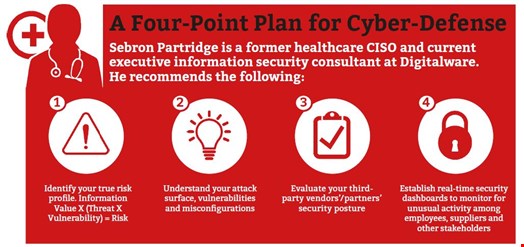
So how do supply chain organizations, pharma companies, governments and other key stakeholders mitigate the risk of cyber-related disruption?
For Nominet’s government cybersecurity expert, Steve Forbes, the best defense is one built around collaboration.
“Not only should the cybersecurity industry be in close contact with pharmaceutical companies, but it should also be integrated within and between governments,” he tells Infosecurity. “Sharing intelligence on attacks and support on mitigation strategies globally will be critical to securing the vaccine supply chain and wider healthcare services.”
Gill agrees, highlighting the UK’s Cyber Security Information Sharing Partnership (CiSP) as a great example of intelligence sharing. Best practices remain invaluable, he adds.
“Good cyber-hygiene and doubling down on cybersecurity awareness across the workforce with robust reporting processes will help early identification of potential threats – particularly around phishing and social engineering,” he argues. “It’s easy to say, but vigilance across the whole business is so important. For example, when a key event or announcement is identified, try to understand what that means not just for the vaccine program as a whole, but also your organization and even your personal role within that organization.”
However, vaccine distribution networks are likely to further increase the complexity of healthcare supply chains, offering dangerous points of weakness, warns Hannigan.
“Even if a vaccine manufacturer has good cybersecurity, they will want to actively monitor their supply chain and look for weak links, especially among smaller companies with less experience.
“Good advice and a sophisticated managed security service will be the answer for most smaller companies. Bigger enterprises will need to take a more advanced approach to monitoring their ecosystem. As always, getting the basics right and changing the company culture on cybersecurity is the most important step,” Hannigan concludes.
For more on this topic, register for Infosecurity'’s upcoming webinar Securing the COVID19 Vaccine & Supply Chain