There’s no honour amongst thieves. Or so the timeless platitude goes. It seems to remain true in the digital realm too, evidenced by an ongoing saga involving a website purporting to sell VPNs, Java exploits, a keylogger pusher and a “reformed” hacker.
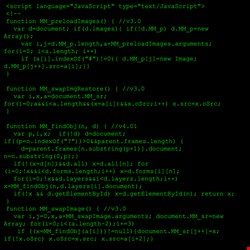
It started with a blog post from Malwarebytes analyst Chris Boyd, focusing on aquavpn(dot)com. Registered anonymously in September 2013, it claimed to be selling VPNs, but was actually serving up a Java exploit kit, which was subsequently thrusting a keylogger onto that system.
De-Anonymizing a Java Crook
Subsequent conversations with an ex-blackhat and former botnet controller going by the name of Trojan7Sec revealed more. He claimed to have hacked the admin panel to the site, which he appeared to confirm in a blog post. He also said he knew someone who had paid to have a Java silent drive-by exploit kit placed on the site. And he was going to dox (de-anonymize) that person.
“He’s using a RAT [remote access Trojan] with no VPN. Oh god”, he said, speaking over Cryptocat.
Trojan7Sec used to carry out similar attacks, at least according to his account of his long history in the game. Why did he want to dox the hacker? “Because he’s hacking people and he’s an embarrassment”, he added, claiming he would soon have the full name and bank details of the owner of the Java drive-by. They have yet to emerge, but Trojan7Sec promised they would be published on his blog soon enough and he would be handing the bank details to the FBI.
It wasn’t just the Java drive-by user he wanted to expose either. He had beef with the registrar for the malicious site, Namecheap. Despite claiming to have lodged at least 18 abuse reports with the company, Namecheap has not taken any action. Namecheap told me it was simply the registrar and had no insight into whether malicious code was running from the site or not.
It recommended I speak with CloudFlare, which provides a content delivery network service for the site, to find out who was hosting the site so I could ask them if they would kill it. CloudFlare said it had flagged the site and associated domains as malicious and contacted the host. But the site remains active. For now, it looks likely to stay live for some time, leaving people looking for a new VPN in danger.
Epic Java Hacks
According to Trojan7Sec, the exploit kit used, Epic Java, was sold on one of the more easily accessible forums. Such kits are less sophisticated than the likes of Blackhole, Magnitude and Sweet Orange, but can still be effective. They are cheap and prevalent too, with one contact telling me they typically sell for between $50 and $70.
A quick search on forums shows there are various models. Indeed, a host of discussions on the pros and cons of the tools can be found, so any prospective buyer has some guidance on what is most effective. One Java drive-by kit, called GalaxyJDB, “has been around for a long time, the people behind it are high quality and know what they're doing, and I wouldn't hesitate to go with them”, says one forum user.
Another responds: “I personally use Epic Java and couldn't be happier with it. The customer support is probably the best I've experienced on these forums. The tools work wonderfully. There's not a single thing I have a problem with when it comes to Epic Java.”
One participant on the thread even appears to point to the malicious Aqua VPN domain, which seems to be offered as part of the Epic Java package: “They had a domain called (name)VPN.com. They also had a girl's blogging or something along those lines domain.”
The Foxy Java drive-by kit also seems to be popular, but one seller said there was little difference between any of them. “I mean what can you differ between two Java downloaders that practically do the same thing? Other than the fact that they will provide more features such as web hosting, and free domains…”
Java Jeopardy
This should all serve as a warning to individuals and companies alike: Java in general remains a serious concern, with vulnerabilities aplenty and various exploit kits targeting them. If it can be disabled, it should be. But for everyone else, they have to rely on the quality of their security protections and the wherewithal of users. The most recent Oracle update fixed a whopping 36 Java vulnerabilities. Fresh ones emerge either on the underground or through more official channels frequently.
Oracle has finally issued one critical update, however, which should protect even the most idiotic of users. When targeting anyone running Java 7u21 and below, those quick and easy Java exploit kits rely on users having to accept a prompt to run an applet, which subsequently makes changes to a victim’s machine. Most know not to accept the applet execution, but even those who do click through should now be protected. Thanks to this January’s update, when the security settings are pushed up to high, Java won’t open any self-signed or unsigned applets, meaning users won’t even be prompted.
So the effectiveness of kits like Epic Java might have been wholly nullified by the latest update, meaning all users should get patching now. As more Java exploit code hits the underground markets, however, those more sophisticated tools will still have the ability to expose weaknesses in Oracle’s kit in silent drive-by attacks. That means Java will remain a favorite point of entry for digital crooks.