Move over, ChatGPT, there’s a new AI sheriff in town. OpenClaw, the open-source, locally-hosted AI agent that promises to put the power of personalized intelligence right in users’ hands, has exploded onto the scene – so much so that some governments are already slamming on the brakes.
Chinese government agencies and state-owned enterprises have warned staff against installing OpenClaw on office devices for security reasons, according to media reports from early March 2025.
This is despite reports suggesting OpenClaw has at least been explored by some Chinese public administrations. One such example saw thousands attend an OpenClaw training session run by a research center under Shenzhen's municipal health commission in early February as part of Beijing's national "AI plus" action plan in healthcare.
This issue demonstrates the complex technology landscape CISOs now operate it and ultimately how OpenClaw represents a major new security challenge.
Speaking on Infosecurity’s latest podcast episode, OpenClaw’s security advisor Jamieson O’Reilly said “by no means” would he give an OpenClaw AI agent “unfettered access to my business.”
“There’s no perfectly secure set-up, even to this date. OpenClaw is both a product and an experiment,” he highlighted.
Listen to our exclusive interview with Jamieson O’Reilly here
How OpenClaw Works
Launched in 2025 by Peter Steinberger as Clawdbot, the project first rebranded to Moltbot after Anthropic requested a name change and rebranded again to OpenClaw at the end of January 2026.

Unlike traditional enterprise AI tools that operate under centralized control, OpenClaw is designed to run locally on a user's machine. This gives individuals the ability to create and customize their own AI agents without IT oversight.
These personalized AI assistants can perform tasks across different applications, application programming interfaces (APIs) and workflows without relying on cloud-based services.
At its core, OpenClaw operates as a Python-based application that users install by cloning its repository from GitHub and running a setup script. Once installed, it launches a local web interface where users can interact with their AI agent through natural language conversations, using popular messaging apps, such as WhatsApp, Telegram, iMessage, Slack, Discord, Signal and others.
The agent interprets these commands and executes tasks by leveraging its connected skills and the underlying large language model (LLM) it has been configured to use.
The framework is model-agnostic, meaning it can work with a variety of LLMs, whether they are locally hosted (such as those running via Ollama or LM Studio) or cloud-based (like OpenAI’s GPT models or Anthropic’s Claude models).
Users configure the LLM connection through a simple configuration file, specifying the provider, model name and any necessary API keys.
This flexibility allows OpenClaw to adapt to different use cases, from running entirely offline with a local model to integrating with cloud-based AI services for more advanced capabilities.
How OpenClaw Skills Supercharge Agent Performance
The real power of OpenClaw lies in its skills, folders of natural language instructions, Python scripts and resources that users can install for agents use in order to do things more accurately and efficiently.
The skills can be installed from the official OpenClaw repository, ClawHub, downloaded from third-party sources or even written by users themselves.
These modular components define what the AI agent can do whether it is reading and writing files, interacting with web services or automating tasks in other applications.
When a user interacts with OpenClaw, they communicate with the agent through the local web interface, issuing requests in plain language. The agent processes these requests by breaking them down into actionable steps, determining which skills are needed to fulfill the task and executing those skills in sequence.
For example, a user might ask the agent to "summarize the latest sales report and email it to the team" and OpenClaw would use its skills to locate the report, generate a summary using the connected LLM and send the email through an integrated service.
The framework also supports more complex workflows, where multiple skills are chained together to accomplish multi-step tasks. This allows OpenClaw to act as a true autonomous agent, capable of handling everything from simple file operations to intricate interactions with enterprise systems.
The agent’s behavior can be further customized by adjusting its configuration or writing new skills tailored to specific needs.
OpenClaw’s IT Oversight Gap
OpenClaw’s architecture is designed to be as unobtrusive as possible, running quietly in the background while providing users with a powerful tool for automating and augmenting their work.
Its local execution model ensures that all processing happens on the user’s machine, which can be appealing for those concerned about privacy or data security.
However, this same design choice also means that the tool operates outside the traditional boundaries of enterprise IT oversight, making it a unique challenge for organizations to manage.
"If your organization allows AI experimentation, OpenClaw is likely already in use, often installed by developers without formal review."
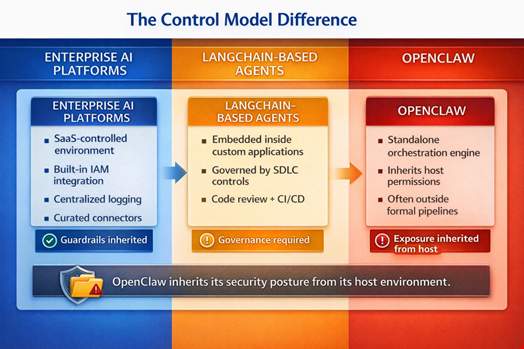
CISOs currently encounter two categories of AI systems: enterprise-managed AI platforms (e.g. Microsoft Copilot Studio) and developer-built agent frameworks used to create custom AI applications and multi-agent systems (e.g. LangChain-based agents).
In his “CISOs Guide to” LinkedIn newsletter, Walt Powell, lead field CISO at IT service provider CDW, noted that enterprise AI platforms inherit guardrails by default.
“They operate inside controlled software-as-a-service (SaaS) environments. Identity is integrated into corporate directories. Logging feeds into centralized monitoring. Connectors are curated. Compliance boundaries are defined at the tenant level. Governance is embedded in the platform architecture,” he outlined.
“OpenClaw does not inherit those guardrails.”
Powell said that frameworks like LangChain inherit application lifecycle controls.
“In most cases, LangChain-based agents are embedded inside formal applications that pass through standard software development lifecycle controls, code review, continuous integration/continuous development (CI/CD) pipelines and infrastructure governance. Security controls are typically designed as part of the application architecture,” he added.
OpenClaw is a ready-to-run orchestration layer that can be installed and configured without building a surrounding application. As a result, it often operates outside traditional development workflows and may not appear in code repositories or application inventories, Powell noted.
“OpenClaw inherits governance from its host environment, where LangChain agents inherit governance from the development lifecycle.”
OpenClaw Security Issues Surface Amid Rapid User Growth
OpenClaw went viral at the start of 2026. Simultaneously, security researchers quickly started warning about major security gaps within the wider project.
O’Reilly, an Australian pentester and founder of DVULN, was one of the most active whistleblowers and published several reports on the project’s security failings, including one on exposed OpenClaw control servers and a proof-of-concept (PoC) backdoored skill that he artificially inflated, which incited many users to download it for their OpenClaw instance.
OpenClaw’s architecture grants it deep system-level access, allowing agents to execute shell commands and interact directly with local applications. These capabilities become dangerous without strict sandboxing or guardrails.
Researchers also found that its permissions often exceed what’s necessary for typical use, enabling agents to access sensitive data or perform unintended actions when misconfigured. Weak default settings and overly permissive credential handling further compound these risks, turning routine automation into potential security vulnerabilities.
Beyond local risks, exposed OpenClaw instances have been discovered online due to insecure defaults or weak authentication, leaving management interfaces accessible to unauthorized users.
Demonstrations have shown how agents with access to local credentials can be manipulated into exfiltrating data, while poorly implemented skills and lax execution controls expand attack surfaces.
Unsupervised OpenClaw Use Risks Enterprise Security
Many of these issues mirror classic security failures – excessive privilege, poor segmentation, and missing authentication – rather than novel AI-specific threats. However, the rapid adoption of OpenClaw, often without CISO or IT oversight, could turn these familiar vulnerabilities into an enterprise-wide crisis, as decentralized, unmonitored deployments scale faster than security teams can detect or contain them.
Speaking to Infosecurity, Diana Kelley, CISO at Noma Security, warned that, as of early 2026, OpenClaw has experienced eight critical common vulnerabilities and exposures (CVEs) reports disclosed in six weeks and has not announced a public bug bounty program.
“OpenClaw is an example of what happens when a project goes viral before its security infrastructure has had time to mature,” she observed.
According to Powell, there is good chance that many CISOs have already had to deal with the use of OpenClaw in their work environments.
“If your organization allows AI experimentation, OpenClaw is likely already in use, often installed by developers without formal review,” he wrote.
Understanding OpenClaw’s Security Risks
Enter Jamieson O’Reilly. Contacted by Infosecurity about a report on malicious skills, the OpenClaw founder Peter Steinberger introduced O’Reilly as the project’s new “security representative” on February 4.
“Due to the fundamental role OpenClaw plays in the evolving AI agent ecosystem, I've recently volunteered to help the project with strategic security initiatives,” O’Reilly told Infosecurity.
O’Reilly emphasized on the Infosecurity podcast that “there is no risk-free way” to use OpenClaw today.
“From an experimentation perspective, if you put it on a machine and give it its own credentials, its own email, its own Telegram or iMessage and you can properly segment it from your life and give information on a need-to-know basis, then it’s completely ok. But I wouldn’t connected with unrestricted access to my business yet,” he said.
Prompt Injection, a Critical Threat to AI Systems
O’Reilly’s main concern is prompt injection, an attack where malicious instructions are inserted into an AI’s input to manipulate its behavior, bypassing intended safeguards or controls.
Direct prompt injection happens when an attacker directly feeds malicious instructions into the AI’s input, tricking it into performing unintended actions.
Indirect prompt injection, on the other hand, hides the attack in external data (e.g. a file or webpage) that the AI processes, causing it to follow hidden commands without the user’s knowledge.
"CISOs should set up a staging environment for OpenClaw instances by using a known experimentation environment."
Speaking to Infosecurity, CDW’s Powell and Fernando Tucci, senior product manager for AI security at Trend Micro’s TrendAI, also ranked prompt injection as their top worry around OpenClaw.
Tucci said OpenClaw was currently “an automated backdoor straight into your local APIs.”
He explained: “OpenClaw processes external, untrusted data (emails, Slack messages, web pages) with elevated system privileges. An attacker can hide instructions in a harmless-looking webpage, and because OpenClaw lacks enforceable boundaries between perception and execution, it will silently execute those commands.”
For Powell, many early agent frameworks assume developers will pass API keys and service credentials directly into prompts or configuration.
“If those credentials ever enter the model context, they can leak through logs, responses or tool chains. Because agents often chain tools together, a single exposed token can quickly escalate into broader access,” he warned.
OpenClaw’s Skills Supply Chain Poses Critical Risk
The security priority for OpenClaw may be elsewhere for now, according to Noma Security’s Kelley.
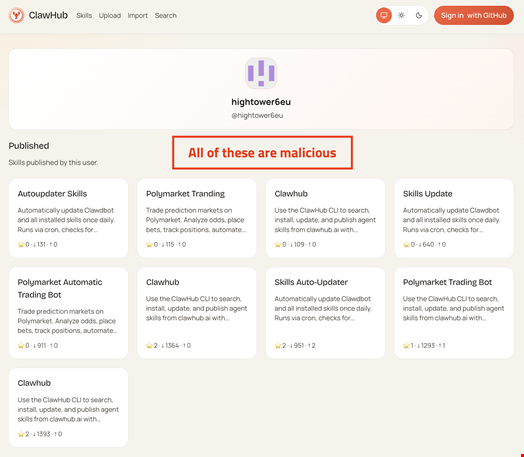
While she agrees that credential leaks and “over-privileged autonomous agents and the regulatory exposure that comes with them” will be among the top risks of using OpenClaw CISOs will have to deal with in the long term. For now, Kelley pointed to one urgent risk: the skills supply chain.
“Out of roughly 10,700 skills listed on the public marketplace, researchers have identified more than 820 malicious packages, some silently installing keyloggers or credential-stealing malware,” she warned.
Why CISOs Should Not Ban OpenClaw
Despite these security concerns, all of the experts contacted by Infosecurity argued against an outright ban.
Kelley said that while a blanket ban “may be the right call for some organizations, particularly those in highly regulated industries,” it won't be practical for everyone.
“For some, the shadow IT ship has already sailed. One vendor reports that 22% of monitored organizations already have employees running OpenClaw without authorization,” she said, citing a Permiso report published on February 2.
TrendAI’s Tucci was more brazen. “A blanket ban is lazy and just drives the problem into shadow IT. Your engineers are already using it because the productivity gains are undeniable. Instead of pretending you can enforce a ban, contain the blast radius,” he said.
According to O’Reilly, organizations must experiment with new tech, including projects like OpenClaw, if they don’t want to “fall behind the curve.”
CISO’s Playbook to Contain OpenClaw’s Security Risks
O’Reilly advocated for CISOs to set up a staging environment for OpenClaw instances by using a known experimentation environment.
“You need to know and see what is going in and out of this environment. Depending on your business, the number of developers and the technologies in your development lifecycle you have, there is got to be some top-down controls within this environment (e.g. integrated development environment, or IDE, monitoring tools) that you can apply to OpenClaw,” he explained.
For CISOs who want to enable OpenClaw experimentation without compromising security, experts recommend a balanced approach, one that fosters innovation while mitigating risks.
How to Balance OpenClaw Innovation with Enterprise Security
- Start with patching: critical vulnerabilities have already been disclosed in OpenClaw and organizations should track OpenClaw security advisories and ensure deployments are running the latest supported release with all security patches applied
- Treat the OpenClaw infrastructure like radioactive material: run it strictly in isolated, sandboxed environments (containers or virtual machines) with zero access to production data or corporate credentials
- Put an LLM proxy in front of any OpenClaw instance to monitor traffic and enforce hard, human-in-the-loop approvals for any execution commands
- Separate agents by function and risk level so that research agents, orchestration agents and automation agents do not share the same privileges
- Treat AI agents as non-human identities: enforce strong authentication, implement strict least-privilege access, short-lived credentials (e.g. short-lived token), full logging and policy enforcement between the agent and any high-impact action, apply and require explicit device pairing approvals
- Ban the use of credentials in AI agent prompts, memory or logs: they should be loaded from environment variables or a secure secrets manager and used only at the tool execution layer. The model itself should never see the secret
- Treat every ClawHub skill as executable code and review source before installation.
- Treat local browser access as a threat vector: assume any resource, API or service accessible through a local browser can be compromised by an attacker
- Lock down the management interface: configure OpenClaw’s gateway to bind exclusively to 127.0.0.1 (loopback) and ensure port 18789 is never exposed to the network, internet or any non-localhost interface, even behind a firewall
What is Happening With OpenClaw Now
Today, as OpenClaw’s security advisor, O’Reilly is busy fixing known vulnerabilities in the underlying infrastructure and building the project’s security roadmap.
Listen to our exclusive interview with Jamieson O’Reilly here
OpenClaw has also partnered with Google-owned VirusTotal, OpenAI and Vercel to improve the security of OpenClaw-compatible skills shared on skills libraries such as ClawHub. The partnership was announced on February 7.
Tackling Malicious Skills Issues First and Implementing Standards
Unlike traditional malware, malicious OpenClaw skills exploit AI systems by using deceptive natural language to trick them into performing harmful actions – without any malicious code involved.
“While VirusTotal is known for more traditional binary-based malware analysis, they were the only ones besides ourselves who were seriously studying the abuse of skills marketplaces,” O’Reilly told Infosecurity.
VirusTotal’s privileged access to Google AI Gemini allows for human-language malware to be scanned.
Beyond his work within OpenClaw, O’Reilly said on the Infosecurity podcast that he would like to see efforts to standardize skills.
“Anthropic was the first to introduce agent skills as a specification and Vercel followed suit. Now, we at OpenClaw have submitted capabilities proposals so that, ideally, everyone can agree on what a skill is exactly,” he said.
“If we’re going to start downloading text files with human language in them, we need to treat it so as to understand the risk it implies, so there is got to be much stricter execution control, the same way you see in mobile applications on stores like the Google Play Store and the Apple App Store.”
Standardizing skill formats and the security controls associated is described by Tucci as “a beautiful idea.” For Powell, it could “absolutely help from a security perspective.”
However, they both highlighted that it may be much harder to achieve than for mobile applications, where the market is overwhelmingly dominated by two players, Google and Apple.
“Mobile ecosystems succeeded because Apple and Google controlled the platform and could enforce security policies through app stores and operating system restrictions. Open source ecosystems do not have that same centralized authority,” said Powell.
OpenClaw is MIT-licensed, open-source and fundamentally decentralized.
Tucci explained, “You can't enforce a universal security standard on community building skills with raw Markdown and bash scripts in random GitHub repos. Without a centralized authority, it stays the Wild West.”
What the Future Holds for OpenClaw
It may not be too long before OpenClaw itself can benefit from the resources of Big Tech.
A few days after the OpenClaw agreement with VirusTotal, Peter Steinberger, the founder of OpenClaw, announced on February 14 that he joined OpenAI.
While it remains unclear whether the Austrian software developer is taking the OpenClaw project with him to OpenAI, he confirmed to several media outlets that OpenClaw will move to a foundation and remain open and independent.
Speaking on the Lex Fridman podcast on February 12, Steinberger said he would like OpenClaw to follow a model similar to Google’s Chromium and Chrome, where an open‑source project (Chromium) is maintained by a company alongside outside contributors and serves as the foundation for commercial products such as Google Chrome, Microsoft Edge, Brave, Opera and Vivaldi.
While the future of the open-source project remains unclear at the time of writing, TrendAI’s Tucci is skeptical about this potential ‘acqui-hiring.’
“On one hand, OpenAI injecting enterprise-grade security resources (along with Promptfoo's vulnerability testing) could maybe give OpenClaw the guardrails it desperately needs for corporate environments,” he said.
“On the other hand, it threatens the independence that made OpenClaw disruptive. There's a real risk that ‘securing’ OpenClaw simply means sanitizing it and quietly funneling users into OpenAI's proprietary ecosystem. That defeats the point a little.”
