Outrage over the Australian Federal Police (AFP) raid at the Australian Broadcasting Corporation (ABC) continues to mount as a question of national security versus freedom of the press plays out between journalists and law enforcement.
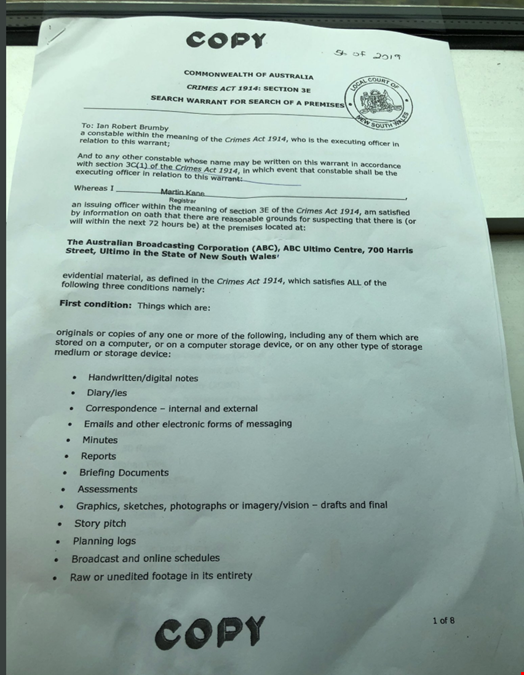
In response to allegations that ABC had published classified information related to stories reported in 2017, the AFP raided ABC’s headquarters in Sydney and seized several documents, according to John Lyons, executive editor at ABC news, who was allowed in the room as several police officers combed through thousands of emails.
“They have downloaded 9,214 documents. I counted them,” Lyons told ABC news in a live interview. “They have set up a huge screen and they are going through email by email. It’s quite extraordinary. I’ve never seen an assault on the media as savage as this one I’ve seen on ABC.”
“The AFP have the power now to be going through those documents and essentially deleting anything they want. They can change material,” said Lyons who live-tweeted events as they unfolded.
The news is the second raid on members of the press in Australia in less than 24 hours. Combined with the recently passed Assistance and Access Bill, also known as the anti-encryption law, these raids are especially troubling. “Australia is heading down a path that leads to its citizens not being able to speak freely nor privately,” said Paul Bischoff, privacy advocate with Comparitech.com.
“When members of the press are targeted by their own governments, it's important for journalists to step up their cybersecurity and protect sources. If you cannot depend on the law to protect press freedoms, then journalists must take care to secure their communications, notes, drafts, data, documents and other materials. Most importantly, they need to encrypt their phones and laptops, connect to reputable virtual private networks (VPNs) and use secure communication channels with end-to-end encryption.”
