Chinese-backed threat actors are increasingly relying on proxy networks known as operational relay boxes (ORBs) to gain an advantage when conducting espionage operations, Mandiant has observed.
This attack tactic allows these advanced persistent threat (APT) groups to raise the cost of defending an enterprise’s network and shift the advantage toward espionage operators by evading detection and complicating attribution.
In a report published on May 22, Google-owned Mandiant described how Chinese nation-state groups, including the infamous Volt Typhoon, leverage ORB networks to deploy cyber espionage campaigns.
How ORBs Can Be Used in Cyber-Attacks
In the realm of cyber espionage, an operational relay box (ORB) network is a covert system employed by intelligence agencies.
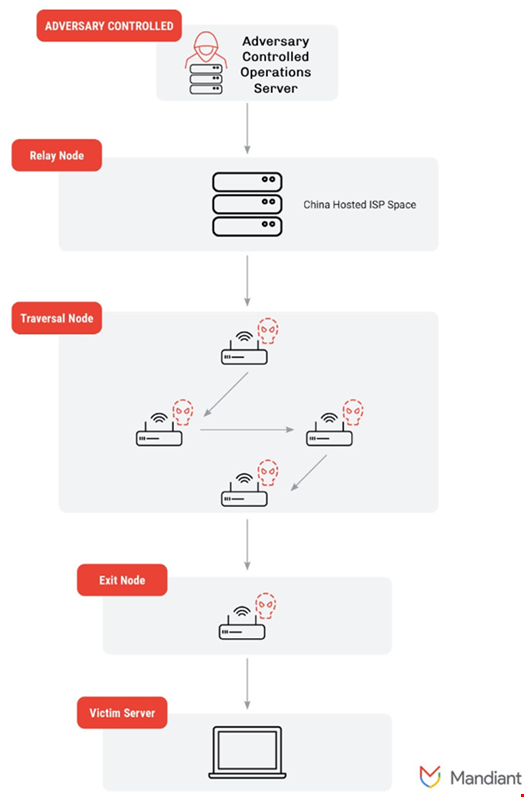
Like bot networks (botnets), ORB networks are mesh networks comprised of compromised devices, including virtual private servers (VPS), Internet of Things (IoT) devices, smart devices and routers. These devices constitute the nodes of the ORB network.
These devices are scattered around the globe and used as proxies for an intelligence service or a cyber espionage group, essentially turning them into secret outposts.
Mandiant classifies ORB networks into two fundamental types:
- Provisioned networks are made up of commercially leased virtual private server space that are managed by ORB administrators (e.g. ORB3, or SPACEHOP, administered by Chinese intelligence services)
- Non-provisioned networks are often made up of compromised and end-of-life router and IoT devices (e.g. ORB1, or ORBWEAVER and ORB2, or FLORAHOX)
It is also possible for an ORB to be a hybrid network combining both leased VPS devices and compromised devices.
ORB administrators rely on autonomous system number (ASN) providers in different parts of the world to reduce exposure or dependence on any one nation’s internet infrastructure.
An ASN identifies a unique network or group of networks on the internet that share a common routing policy and are managed by a single administrative entity. Most ASNs are allocated to network operators (internet service providers, mobile network operators…), although other entities like research labs, military services and universities also have distinctive ASNs.
Read more: CISA Warns Critical Infrastructure Leaders of Volt Typhoon
ORBs create a network interface, administer a network of compromised nodes, and contract access to those networks to multiple APT actors that will use the ORB networks to carry out their own distinct espionage and reconnaissance.
These networks are not controlled by the APT actors but rather are temporarily used by them, often to deploy custom tooling more conventionally attributable to known China-nexus adversaries.
Why Chinese Hackers Use ORBs
Although the use of ORB networks by cyber espionage actors is not new, their generalized use by a multitude of China-nexus espionage actors has become more common over recent years.
By using these mesh networks to conduct espionage operations, these threat actors can disguise external traffic between command and control (C2) infrastructure and victim environments, including vulnerable edge devices exploited via zero-day vulnerabilities.
Mandiant noted that the adversary-controlled operations servers (ACOS) and relay nodes are most commonly hosted in China-affiliated and Hong Kong-based IP space. The rest of the nodes can be located elsewhere on the planet.
In the report, the Mandiant researchers assessed with moderate confidence that this is an effort to raise the cost of defending an enterprise’s network and shift the advantage toward espionage operators by evading detection and complicating attribution.
An example of the global distribution of an ORB network can be seen in what Mandiant tracks as ORB3 or SPACEHOP, an active network leveraged by multiple China-nexus threat actors.
The high volume of APT-related traffic through globally distributed nodes indicates that this network targets a wide array of geographic targets co-located in the geographies of observed exit nodes, including the US, Europe and the Middle East.
The increased use of ORBs by Chinese threat actors brings the following challenges for defenders:
- Indicators of compromise (IOCs) are increasingly useless as threat actors cycle through network infrastructure
- Actors' traffic can originate from a geographic origin that appears typical and doesn’t raise red flags
- Attribution based on network infrastructure is impossible because multiple actors are sharing infrastructure provided by individual contractors and others
If network defenders can shift the current enterprise defense paradigm away from treating adversary infrastructure like IOCs and instead toward tracking ORBs like evolving entities akin to APT groups, enterprises can contend with the rising challenge of ORB networks in the threat landscape, Mandiant believes.
“The rise of the ORB industry in China points to long-term investments in equipping China-nexus cyber operators with more sophisticated tactics and tools that facilitate enterprise exploitation to achieve higher success rates in gaining and maintaining access to high-value networks,” Mandiant said.
“Whether defenders will rise to this challenge depends on enterprises applying the same deep tactical focus to tracking ORB networks as has been done for APTs over the last 15 years,” the Mandiant report concluded.
Read more: China Presents Defining Challenge to Global Cybersecurity, Says GCHQ