Iran-linked threat actors are targeting high-profile researchers working on the Israel-Hamas conflict via a sophisticated social engineering campaign, according to Microsoft Threat Intelligence.
The threat actor Mint Sandstorm (AKA APT35 and Charming Kitten), which has ties to Iranian military intelligence, is using bespoke phishing lures to entice targets into downloading malicious files, with the aim of stealing sensitive data.
The ongoing campaign, which was first spotted in November 2023, is targeting experts deemed to have the potential to influence intelligence and policies in areas of interest to the Islamic Republic of Iran.
Microsoft believe this campaign could be designed to gather different perspectives on the Israel-Hamas conflict from individuals across the ideological spectrum.
The targets primarily work at universities and research organizations in Belgium, France, Gaza, Israel, the UK and US.
How Mint Sandstorm is Targeting Middle East Experts
Microsoft said it has observed new tactics, techniques and procedures (TTP) being utilized by Mint Sandstorm in this campaign, including the use of legitimate but compromised email accounts to send phishing lures.
Initially, the threat actor emails the target pretending to be a high-profile individual, such as a journalist at a reputable news outlet requesting input for an article about the Israel-Hamas war.
In some cases, the email address used to send the message is spoofed to resemble a personal email account of the individual they are spoofing.
In others, legitimate but compromised email accounts belonging to the impersonated individual are used.
The first message is benign and contains no malicious content, with the aim of building trust with the victim, according to Microsoft’s Threat Intelligence Team. The use of legitimate email accounts likely bolsters Mint Sandstorm’s credibility.
If the target agrees to review an article or document referenced in the initial email, the Iran-linked attackers follow up with an email containing a link to a malicious domain.
These domains host a RAR archive file purporting to contain the draft document. Once opened, the .rar. decompresses into a double extension file with the same name.
When this file is opened, it runs a curl command to retrieve a series of malicious files from subdomains owned by Mint Sandstorm, glitch[.]me and supabase[.]co.
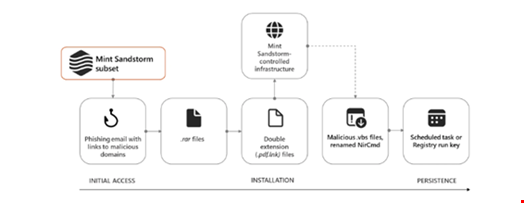
Multiple malicious file types are downloaded to targets’ devices in this campaign, Microsoft said. This includes a renamed version of legitimate command line tool NirCmd, which allows a number of actions to be carried out on a device without displaying a user interface.
A new custom backdoor, MediaPI, has been observed sending encrypted communications to Mint Sandstorm’s command-and-control (C2). This file masquerades as the legitimate Windows Media Player application. Communications to and from MediaPl’s C2 server are AES CBC encrypted and Base64 encoded, and the file is able to terminate itself.
Attackers were also observed writing activity from victims’ devices to a series of text files, including one named documentLoger.txt.
The Microsoft team emphasized the sophisticated nature of the campaign, which makes it difficult for victims to detect.
“Operators associated with this subgroup of Mint Sandstorm are patient and highly skilled social engineers whose tradecraft lacks many of the hallmarks that allow users to quickly identify phishing emails,” the Microsoft blog read.
Protecting Against the Mint Sandstorm Campaign
Microsoft set out the following recommendations for universities and organizations involved in research in Middle East affairs to protect against the phishing emails used in this campaign:
- Train end users against clicking URLs in unsolicited messages and disclosing their credentials. This includes checking for poor spelling and grammar and spoofed app names, logos and domain URLs appearing to originate from legitimate applications or companies
- Use tools that are able to identify and block connections to malicious domains and IP addresses
- Turn on cloud-based machine learning protections to block new and unknown malware
