A threat actor has been distributing remote access Trojans (RATs) on Android and Windows operating systems using online meeting lures, according to cloud security provider Zscaler.
This campaign has been ongoing since at least December 2023, observed Zscaler’s threat intelligence team, ThreatLabz.
The distributed RATs include Android-focused SpyNote RAT and Windows-focused NjRAT and DCRat.
Malicious APKs and BAT Files Leading to RAT Payloads
To lure its victims into downloading the RATs, the threat actor created several fake online meeting sites, impersonating brands like Microsoft-owned Skype, Google Meet and Zoom.
“All of the fake sites were in Russian,” noted Zscaler ThreatLabz researchers.
The attacker utilized shared web hosting services to host all these websites on a single IP address. The first one was created in early December 2023 with a URL that resembles the legitimate Skype URL.
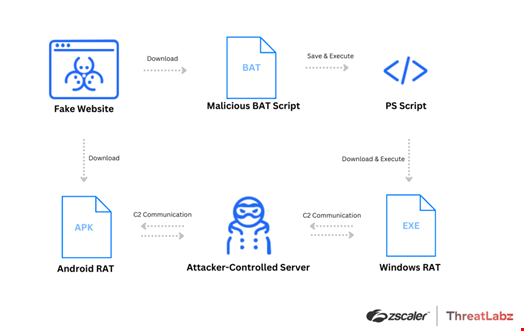
When a user visits one of the fake sites, clicking on the Android button initiates the download of a malicious APK file, while clicking on the Windows button triggers the download of a BAT file, a script in Windows that automates tasks. When executed, this BAT file performs additional actions, ultimately leading to the download of a RAT payload.
In some cases, an Apple App Store button is also available. However, this button redirects to https://go.skype.com/skype.download.for.phone.iphone, indicating that the threat actor was not targeting iOS users with malware.
The three RATs hosted by the threat actor, SpyNote RAT, NjRAT and DCRat, can steal confidential information and files and log keystrokes.