![Steven Sprague on Windows 8: "[It] can be configured to be the most secure Windows OS ever"](https://assets.infosecurity-magazine.com/content/float/ca283957-fdb6-4a65-8f73-8a5e4b965cea.jpg)
When it comes to user experience, Windows 8 fancies itself as the matrimonial confluence of mobile and desktop computing. How it looks and feels to users, however, is irrelevant to this discussion. Sure, there are some elements of the Windows 8 ‘experience’ that are germane to any assessment, but the purpose here is to evaluate its new security features, especially those useful in the enterprise setting.
The OS will be offered in three primary flavors: the conventional ‘home’ edition for consumers, Windows 8 Pro for enterprises, and Windows RT for ARM (mobile) devices. Most experts agree that Microsoft has hardened its latest OS using a layered approach that combats malware threats at numerous levels. And while possibilities to exploit flaws in the OS will undoubtedly surface, the verdict in this case appears to be that Microsoft has taken Windows 8 in a more secure direction.
Seal of Approval
Windows 8 marks Microsoft’s official transition from BIOS firmware to the consortium-backed Unified Extensible Firmware Interface, or UEFI. The company now requires all manufacturers shipping Windows 8 devices replace the pre-boot BIOS firmware with UEFI.
Perhaps more controversial to miffed Linux lovers is the Secure Boot feature of Windows. Secure Boot intends to block rootkit malware from infecting a system by preventing a machine from executing what is known as ‘bootloader’ code. All code running during the boot process must be verified through a digitally signed certificate from a key stored in the UEFI firmware.
Rootkit malware, as the name implies, allows ‘root’ access to a machine at start-up, complete with most administrative privileges. Rootkits, furthermore, often run on a system undetected using numerous obfuscation techniques.
“By using this capability [Secure Boot], the firmware can verify software before it runs and make sure that no untrusted code runs before the operating system is loaded”, Microsoft wrote in its UEFI white paper, adding that it “enables the operating system to establish a security foundation for all the other software on the computer”. Of course, this means software makers will need to comply with the UEFI framework by getting their certificates verified by Microsoft and thereby receive its ‘Designed for Windows 8’ seal of approval. It’s perhaps a drag on consumer choice and innovation, but undoubtedly a security plus. The aforementioned Linux fans may find it difficult to run their operating system on a Windows 8 PC, but that’s a user experience issue, and not a security one.
The added security features are, of themselves, worth the upgrade to Windows 8 according to Paul Henry, a computer forensic analyst and evangelist for security firm Lumension. “I really like UEFI Secure Boot”, Henry said enthusiastically. “You have some great rootkit protection there.”
Similar praise was lauded by Stephen Sprague, CEO of Wave Systems, a firm that specializes in hardware-based security. “Microsoft has also added ELAM, or Early Launch Anti-Malware, which starts a portion of the anti-virus early on in the boot process before any drivers on a machine are loaded”, which he says confirms the anti-virus is signed, trusted code. “Now you can assure the baseline of your operating system and anti-malware engine as known code.” Sprague also says this switch in boot order, which runs ELAM first, helps harden the OS.
The new boot process does seem to create a more secure operating system in the opinion of Kevin Curran, senior member of IEEE and a reader in computer science at the University of Ulster. “It is an attempt to secure [the device] at a root level, where it should be secured before the operating system kicks in”, he commented.
Protection Out of the Box
Windows 8 is unique because it is the first operating system to come with a free anti-malware product straight out of the package: Microsoft’s own Windows Defender. It can be disabled to install commercial versions of anti-virus/malware software, but Windows Defender will be active out of the box.
Another enhancement includes the Smart Screen filter, which first shipped with Internet Explorer 9. It will come pre-installed in Windows 8 and works with any browser, not just IE. The alert screen first checks a program you want to download against Microsoft’s Application Reputation filter, which uses a reputation-based algorithm.
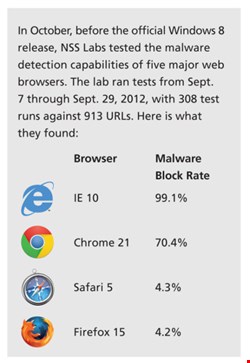
The App Rep feature works with in conjunction with the Smart Screen web alerts and the system’s Download Manager to educate users about downloading potentially malicious software. Before its official release, NSS Labs tested the malware detection effectiveness of IE 10 pre-installed on Windows 8. It found the browser vastly outperformed Firefox, Chrome, and Safari in detecting potentially compromised URLs based on reputation (see graphic).
Other evaluations were not so flattering. BitDefender, an anti-virus vendor, did its own assessment, evaluating Windows Defender against 100 of the most widely used malware families. It found the pre-installed anti-malware suite failed to detect 15% of the samples.
“As a means of protecting a computer from viruses, data theft, and other types of malware, Windows Defender is better than nothing”, wrote the firm’s chief security strategist, Catalin Cosoi, in an email to Infosecurity. “But it’s not a whole lot better”, he added.
BitDefender’s own assessment, nonetheless, failed to hit on another related point: 234 of the 385 malware samples the firm tested against devices without Windows Defender installed were able to successfully infect it. The score sheet here presents some simple math – a 15% failed detection rate with Windows Defender versus a 60.8% infection rate without it.
“Most of the popular anti-virus systems can do better”, Cosoi asserted, which may be entirely true. But if you ask Paul Henry, in his opinion Windows Defender outpaces some commercial anti-virus offerings.
Henry points to a report by AV-Comparatives, an independent Austria-based non-profit that analyzes anti-virus software. An October 2012 report compared 18 commercial AV products (McAfee, Sophos, Trend Micro, and Webroot did not participate) and found that the Windows Defender had a higher detection rate than four other paid AV suites.
Most of the paid versions did outperform Microsoft’s free AV, but not all of them. Contrary to the criticism, it appears that something is ‘a whole lot better’ than nothing, even if it’s free.
“For a new offering…Windows Defender is sure to raise the bar in AV product offerings”, Henry noted in his assessment. “[It] is poised to offer better protection than many commercial AV products.”
Curran’s assessment of Windows Defender is more tempered. “It’s a good thing”, he said, channeling his inner Martha Stewart. Even for a self-proclaimed ‘computer geek’ like Curran, he told me it’s hard to determine the level of protection these AV products provide. Nonetheless, he applauded the pre-installed anti-malware on Windows 8 as a welcomed addition.
Richard Edwards also kicked the tires on Windows 8. The principal analyst with research firm Ovum determined both Defender and Smart Screen to be security pluses. He noted the pre-installed anti-malware is particularly useful in mid-sized and small businesses, but that larger enterprises with IT security teams will continue using third-party products to combat malware and fill in the gaps where Defender falls short.
“Microsoft is using this feature to aim primarily at the consumer market”, he stated while predicting that, at the smaller end of the enterprise market, “it will be appreciated more”, where some will accept the risk and forgo paid AV solutions.
And Some of the Rest…
There are a handful of other security features new to Windows 8, including many that are useful in an enterprise setting. One application security feature caught the eye of Wolfgang Kandek, CTO of security firm Qualys. “Memory Management in Windows 8 has been re-architected to provide additional safeguards, such as comprehensive randomization”, he wrote in an email to Infosecurity.
Kandek is alluding to a security measure known as Address Space Layout Randomization, or ASLR, which randomizes the location of a program’s executable commands within the device memory to defend against exploits. “Most of the memory exploit tactics, such as heap sprays, that attackers use to gain control of a Windows 7 machine will now fail under Windows 8, which benefits all applications running on [it]”, he observed.
Windows 8 will also integrate support for encryption tools, such as self-encrypted drives and Trusted Platform Modules (TPM). TPM is a hardware-based specification detailing a secure crypto processor that can store keys used to protect information. It has the potential to transform enterprise authentication according to Sprague.
With TPM, whenever a device is connected, it is managed by the enterprise, he asserted. “The central infrastructure now has a token held in hardware that is part of my network access, when I turn the machine on – every time. It’s been launched as part of Windows 8, and Microsoft has supplied the infrastructure to support TPM”, Sprague noted.
Henry admitted that TPM hasn’t had much traction to date, but nonetheless declared his approval for the concept. “It ties everything to the hardware itself”, he articulated. “There are some administrative burdens” to TPM, Henry said, which requires the backing up of hardware. “But over time it will probably catch on”, he predicted.
“TPM has been around for so long, but it has never really had traction in the [computing] community”, observed a more skeptical Kevin Curran. It’s interesting, he noted, “but I don’t see it making any difference in the market”.
Slipping through the Cracks
A handful of vulnerabilities were discovered during the Windows 8 testing period, but Microsoft has had plenty of time to patch these. More will be found, and more yet will be patched. Lather, rinse, repeat. After all, as with any operating system, bugs will always find a crack no matter how much effort is spent on keeping them out.
“Technically the attack surface in Windows 8 is bigger than in Windows”, wrote Prashant Gupta, a security architect for McAfee Labs, during his pre-release testing. He specifically cited drastic changes in the Windows 8 user interface designed to provide a more seamless mobile-to-desktop experience, but concluded that this increased attack surface was offset by “significant checks and measures put in place” by Microsoft.
| "Vulnerabilities won’t go away because Microsoft releases Windows 8 – they will always be here, and it’s a simple fact of life" |
| Paul Henry, forensic analyst |
The company’s application marketplace, Microsoft Store, brings with it a lauded app vetting process, and Windows 8 combines this with the ability to restrict an installed application’s access to device resources. Yet something like application verification is not entirely fool proof – Apple’s iOS and Android both have the scars to prove this.
Microsoft’s OS still dominates the enterprise computing market, and the Microsoft Store’s integration into Windows 8 may spell the end for software in a box, as James Lyne, director of technology strategy at security firm Sophos, observed. “While the Windows Store will be secured, that doesn’t mean that malicious apps can’t slip through.” Further, Lyne continued, existing security and monitoring tools may be impacted when applications are purchased through it: “for example, an application historically delivered as an executable could now be entirely web-based”.
Most Secure Windows Ever?
The short answer is yes. The long view holds that whatever OS comes next will also be the most secure, and so on after that. The jury we impaneled provided a similar verdict.
Kevin Curran wholeheartedly agrees that Windows 8 is the most secure version of the OS to date. In addition to the aforementioned upgrades, he cites the many enterprise-related security features available in Windows 8 Pro – among them, self-encrypting drive capabilities and multiple BitLocker offerings.
Security researchers on the Twittersphere lamented the downfall of many zero-day exploits that once worked on Windows 7, but are now no longer useful on Windows 8. This was the observation of Paul Henry, who reiterated his belief that the latest incarnation of Windows is an unquestionable security upgrade.
“Vulnerabilities won’t go away because Microsoft releases Windows 8 – they will always be here, and it’s a simple fact of life”, he cautions. “The real measure here will be how quickly Microsoft responds to handle issues” that do emerge.
Richard Edwards at Ovum concurred, and declared Windows 8 is the most secure version of any OS to date. “Nobody would expect Microsoft to go backwards”, he told me, citing Windows RT for mobiles as perhaps the most secure model. “New devices that will ship with the TPM module and Windows 8 installed certainly does address the issue of risk related to being rooted by sophisticated malware products”.
“Windows 8 can be configured to be the most secure Windows OS ever”, says Steven Sprague, highlighting the ability of TPM to eliminate the need for human-based user credentials. Most important, he said in closing, the “network is moving from connections to identity”. Windows 8, with its support for TPM Sprague remarked, means an enterprise can own and control all devices moving on its network.
Edwards considers the introduction of Windows 7, and now version 8, to be a watershed moment in OS security. “There are a large number of companies still running on Windows XP, wondering if they should move to Windows 7 or Windows 8”, he acknowledged. “They will be glad to know that security is tighter all around”.
The features and commentary in this review are just a few examples of the security enhancements that Microsoft has rolled out with Windows 8. The topics covered are not all-encompassing, and I regret being unable to discuss some of them more in-depth. This being said, I attempted to pick out the ones that appeared most novel, most interesting and – for our readers’ sake – most relevant to their working lives.
Most, if not all of you reading this, are highly educated consumers when it comes to security, and Microsoft – Lord of the Enterprise – knows this as well. The company realizes you expect each successive version of Windows to be safer and easier to use than its predecessor. If they can make your life simpler – and your CIO’s – then Microsoft gets to keep another customer. With Windows 8, it appears the software giant is no longer playing for keeps, but is instead seeking to reclaim some of the market.