Infosecurity News

FitMetrix Exposes “Millions” of Customers’ Data
Unprotected cloud database again to blame
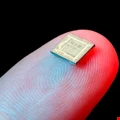
US Telco Finds Evidence of Supply Chain Alteration: Report
Bloomberg doubles down with latest Supermicro allegations

Mozilla Delay Distrust with Continued Symantec Certificate Use
Continued widespread use of Symantec certificates has led to Mozilla to delay Firefox updates

One in 10 Reported Emails Verified as Malicious
Phishing resiliency on the rise as reporting rates increase

Sharp Rise in Young Brits Becoming Money Mules
Cifas stats also reveal more under-21s are victims of fraud

Volume of Stolen Credentials Soars 141% in North America
Blueliv stats reveal declines in other regions this year

US Arrests Alleged Chinese Spy
DoJ claims MSS operative tried to steal aviation secrets

#ISC2Congress: The Promise of Blockchain
At the 2018 Security Congress, experts from CA Technologies say blockchain is revolutionizing cybersecurity.

#ISC2Congress: Soft Skills Take Front Seat
A networking collaboration event at Security Congress 2018 focuses on inclusion and diversity.

#ISC2Congress: Role-Play Brings Security to DevOps
Securing DevOps requires communicating with people.

Morrisons Appeals Insider Breach Compensation Ruling
UK Supermarket chain says it should not be liable for compensation

Magecart Hits Popular Customer Review Plugin
Supply chain attack stopped early after quick work from Shopper Approved

Microsoft Fixes Zero Day and Data Deletion Bugs
Relatively light autumn patch load for admins

#ISC2Congress: Threats to Enterprises Just Starting
What you’re fighting now is going to get worse, says Attivo Networks’ Tony Cole at Security Congress 2018.

#ISC2Congress Honors Grassroot Cyber-Safety Effort
Education day at Security Congress focuses on promoting education in the community.

#ISC2Congress Makes Cyber Matter with Garfield
Security Congress welcomes Garfield with a focus on cybersecurity safety and education.

Centrify Spins Out IDaaS into new Vendor Idaptive
Centrify has spun out its Identity-as-a-Service (IDaaS) service into a new company, which it has named Idaptive

BBC Reports Over 170 Devices Lost or Stolen
Past two years saw devices costing over £100K go missing

Google+ Set to Close After Privacy Snafu
An estimated 500,000 users had profile data exposed

Heathrow Fined £120,000 After Losing Thumb Drive
ICO uncovered serious data protection deficiencies



