

At the end of last year, a Check Point survey of IT managers and senior IT staff revealed that 55% of those questioned knew of employees using personal smartphones for work purposes, and 39% admitted their companies had no formal security deployment process for such devices. With the most recent Juniper Research forecast from June 2011 indicating that less than one in 20 smartphones have third-party security software installed, isn’t it about time you started taking smartphone security seriously?
Believe the Hype?
The trouble with ‘mobile phone security’ is that, as a genre, it has suffered from being somewhat overhyped for many years. When, and how then, have things changed? John Stringer, senior product manager at Sophos, is surprisingly candid in admitting that there has been “a lot of puff about mobile phone security in the past”, but points out that much of those hyped concerns are now proving to be valid as smartphones and tablets become ubiquitous, and platform providers encourage easy app development and release systems. “We can draw a clear parallel between the growth of Android as the dominant mobile operating system and Windows…based on the sheer volume of people using the platform.” This, Stringer insists, is why Android has become an attractive target for hackers.
What about BlackBerry? The common perception that the platform is more secure than Android might be not be entirely accurate, according to Ron Gula, CEO of Tenable Network Security. “The reality is that BlackBerry does have more enterprise features and controls such as remote kill, email retention, guaranteed message delivery, with application and encryption controls”, Gula told Infosecurity. “While this is important”, he continued, “a lot of it is just details, and we’ll probably see some leapfrogging between the various mobile vendors as they get bitten and react.”
| "Security policies should be applicable to any device used for accessing corporate data" |
| Chris Witeck, iPass |
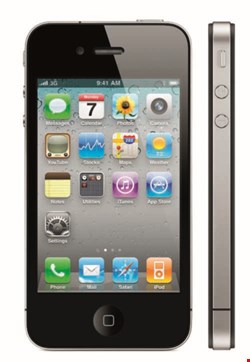
Then there’s Apple – often described as most secure of all, but even iOS has its security problems. “With Apple iOS’ lack of a file system, iPhone and iPad users are increasingly taking advantage of insecure and unmanaged cloud-based consumer services to share confidential information and collaborate with people outside the organization”, warns Paula Skokowski, chief marketing officer with Accellion. They do so, she says, “with little to no regard for corporate and IT security policies”. The main problem, she explains, is that these consumer-grade solutions allow individuals to share, send and sync files between devices, yet leave IT and security teams with no visibility into the sharing of enterprise data.
The Smart Nature of Mobile Risk
So what is the nature of the smartphone risk at the moment then? Perhaps the most honest answer is ‘minimal’, assuming that smartphones are protected correctly in the first place with organizations deploying devices to staff who are aware of the risks and take steps to mitigate them. “The real risk comes when an organization does not fully control personal device usage”, warns Check Point’s head of Western Europe sales, Nick Lowe. “That’s when corporate data starts finding its way to unauthorized devices that are outside of the IT team’s control, and smartphones are very easily lost or stolen”, he says.
As global VP for the Information Security Forum (ISF), Steve Durbin cautions that many smartphone devices were not originally designed as business tools, and as a consequence, “do not offer levels of security comparable to current desktop and laptop computers”. This, he says, is a huge problem in the way they are being used, because it is “blurring the lines between personal and business usage and behavior”.
| "The real security issue rests with the platforms they run on" |
| Bill Weinberg, OK Labs |
There’s little doubting that a smartphone can expose a business to many risks, including malware, for example. The highest risk of exposure to malware still currently sits squarely with Nokia’s Symbian OS which is – perhaps thankfully – experiencing plummeting market share. Smartphone malware, however, is not in decline. “Google Android’s market share is taking off, so the risk of mobile malware is transferring from Symbian to Android-based devices”, warns John Stringer.
Stringer does admit that hype surrounding smartphone malware should be avoided, as there are ‘only’ hundreds of known malware types on Android compared with hundreds of thousands per day for the wider Windows OS. “The big question is whether the security risk will ever get as bad as it has on Windows”, Stringer tells us, before answering his own question. “The jury is still out, but in all likelihood it probably won’t. The bad guys have much more to gain for much less work by targeting central repositories of data stored on web servers or within SQL databases.” Of course, the deployment and downloading of poorly tested (and coded) apps remains the other big smartphone security risk (see box at end of this article).
Bracing Yourself for the Smartphone Security Flood
So that’s the situation now. But, what’s next? What should infosec professionals be readying themselves for in terms of the next stage in the evolution of smartphone security risk? Max Taylor, corporate marketing director at Orange, reckons we should think sideways and look at the uptake of Internet Protocol version 6 (IPv6), which will bring better security to businesses. “IPv6 might also introduce some security considerations”, Taylor says.
“The growing internet user base is likely to increase the number of phishing sites on the network and it may become more complicated to protect your business.” Taylor suggests looking at getting on top of encryption for mobile devices, and encrypting data in transit.
Neill Duff, a senior vice president at Entrust, thinks that infosec professionals will be more tied up with having to deal with the challenge of multiple platforms, and multiple ownerships. “Forrester stated that 50% of firms have embraced a multi-platform mobile strategy”, he says. “Across all industries, information security professionals are already struggling to maintain security while allowing these mobile devices on the network.”
Consumerization of the Workplace
Consumerization is undoubtedly a problem, but what can be done to safeguard against this growing risk when the asset management infrastructure for mobile devices is much less mature than it is for PCs? Dale Gonzales, director of engineering at Dell SecureWorks, refers to the problem of patching as just one example of the problems being faced. “Once a vulnerability is discovered, the OS vendor has to fix it. Once the OS vendor has fixed it, the fix has to be distributed to hardware vendors”, Gonzales explains. “Once the hardware vendors have tested/incorporated the fix, often the carrier has to distribute/release the patched OS.” Overall then, it can be difficult to track what’s been discovered, what’s been fixed, where the fix is in the patch cycle, and which users have patched their phones.
Malcolm Marshall, head of information security at KPMG, admits that “devices owned by employees present a unique set of configuration challenges”, and points in particular to the “right to control personal devices, which is not yet entirely clear.”
| "With Apple iOS’ lack of a file system, iPhone and iPad users are increasingly taking advantage of insecure and unmanaged cloud-based consumer services" |
| Paula Skokowski, Accellion |
Chris Witeck, iPass’ director of product marketing, doesn’t necessarily agree. “One thing we’ve seen organizations do is treat security on a consumer device differently than on an IT-managed device”, he told us. “This should not happen; security policies should be applicable to any device used for accessing corporate data.”
iPass’ Witeck argues that the IT department has every right to allow different levels of access based on device type, user role and whether the device is IT managed or not.
Gord Boyce, CEO of ForeScout, agrees and suggests installing a network access control (NAC) solution. “NAC can identify users and their mobile devices”, Boyce explains, adding that it “force[s] guest registration, as well as appl[ies] policy to users and device types in order to limit access to appropriate network resources only.”
Entrust’s Duff believes that infosec professionals should “attempt to determine what supported platforms they accept and build security and access strategies” by adopting the following strategy:
- Merge access management strategies/policies with mobile management strategies
- Leverage mobile devices to enhance access management across the organization
- Build an information control strategy for devices based on platform
- Create a mobile device management strategy/capability
- Merge security and mobile IT operations
Everyone is aware of the need to meet the increasing demand of smartphones – and tablets for that matter – accessing the network, but is there really a one-size-fits-all solution to minimize the security risk? Not according to Duff, who insists there is “no silver bullet for mobile device management”.
Is the smartphone app security problem entirely down to poor coding, or is that too harsh a criticism of mobile developers? Dave Schneider, senior manager of market development with Ixia, reckons that mobile application development environments are actually excellent, making it pretty straightforward for new programmers to develop valuable business applications. “We haven’t seen this type of marketplace in quite a few years”, Schneider explains, warning “to date, good programming practice and defensive programming haven’t been a top concern of developers. This will soon lead to exploits that take advantage of the immaturity of the developers.” Bill Weinberg, a virtualization expert who works with Open Kernel Labs (OK Labs) disagrees, telling us that while application developers as a group could probably be more security conscious, “the real security issue rests with the platforms they run on”. Weinberg argues that application platforms should treat all third-party apps as untrusted and incorporate a strong isolation architecture. “While leading mobile OS/app platforms in most cases do take advantage of native OS programming models (Linux processes underlying Android Dalvik programs), even those mechanisms leave room for a range of exploits”, Weinberg insists. He argues that it is the platform’s responsibility to implement:
|