The concept of an ‘infosec rock star’ or industry celebrity isn’t new, but social media has certainly thrown open the doors to auditions, allowing aspirations of notoriety to spread like a disease. Eleanor Dallaway unpacks the industry’s obsession with fame
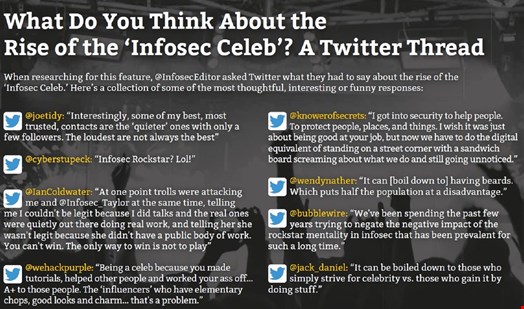
For decades, the information security industry has adorned a few individuals with the label ‘infosec rock star’ or ‘infosec celeb.’ To some, those terms are laughable, while others buy into that industry stardom. Less debated, however, is that whatever term you’re comfortable affording to the well-known people in the industry, the proliferation of this trend, or indeed culture, has absolutely intensified.
Before social media, industry professionals earned their ‘celebrity’ status through speaking engagements at industry events. Some have even pointed to the advent of hacker culture and communities on BBSs and IRC channels, where members would compete to earn notoriety.
“It started with DEF CON and Black Hat always booking the same speakers, like the legendary Dan Kaminsky and creative speakers like Richard Thieme,” recalls Katie Moussouris. Despite a Twitter following of 110,000 and being highly respected by anyone who knows anything about information security, Moussouris is keen to point out, “I’m no rock star, except maybe at karaoke.” (For more on that, click here)
Jack Daniel, a man as well known to the cybersecurity industry as his namesake spirit is to whiskey drinkers, also refers back to the conference circuit as the advent of infosec stardom. “The antics and exploits onstage at DEF CON and Black Hat advanced this obsession with infosec ‘celebs,’” recalls Daniel. He also points to Kevin Mitnick, who advertises himself as ‘the world’s most famous hacker.’
"I don't know anything about music. In my line you don't have to" - Elvis Presley
The beauty of infosec stardom having its routes in the conference circuit, explains Regina Bluman, security analyst at Algolia, is that it was easy to find “people to look up to, or listen to, based on their contributions, their knowledge and what they’d achieved.” Bluman recalls attending her first infosec conference and watching Jenny Radcliffe and Rik Ferguson speak. “They were part of the reason I got into the industry, but that doesn’t mean I blindly follow and agree with everything they say.”
"There's a difference between amplifying your work through social media and other exposure and just seeking to amplify yourself"Jack Daniel
In contrast, she explains, “social media means that people are put in front of you just because they’re active online. They become infosec famous just for the sake of it.”
The explosion of social media has made it easier to build an audience. Yet there’s not always a correlation between those who gain the largest following and those truly deserving of notoriety. As James Bore, director at Bores Security Consultancy, states, “There’s a saying about those who seek power being the least suitable to hold it, and I really think that applies here.”
For some, ‘infosec celebrity’ has almost become a role that they aspire to, or going one step further, perceive to be a career. “While some are [genuinely] seeking to engage, educate and help others, some are more interested in their own careers and egos. Telling the difference can be hard for those in the [infosec] community, let alone those outside it,” Bore says.
Jack Daniel doesn’t believe that ‘infosec celeb’ is a career path by itself, but he does contend that “it can be part of a career journey.” However, his counter to this point is undeniably poignant. “There’s a difference between amplifying your work through social media and other exposure and just seeking to amplify yourself.” There’s no denying that while the former is healthy, the latter is venomous.
Lisa Forte, partner at Red Goat Cyber Security and co-founder of Respect in Security, believes that this new social media era of pursuit of infosec stardom is beyond toxic. “It’s actually worse than wanting to be a celeb. It’s wanting to have loads of followers, which is something that neither equates to skill or talent.” Follower numbers, she says, neither have value nor are indicative of skill. Indeed, follower numbers are little more than a numerical value that social platforms try to convince their customers equate to success.
Yet, in an industry adorned with highly intelligent people, there is no denying that those with the largest platforms receive kudos. It’s why you see many of the same well-known names on the speaking circuit. “I don’t understand how this industry makes infosec stardom such a thing. I think people will eventually snap out of it and work out that it doesn’t matter,” says Bluman.
Interestingly, Bluman points to the ‘Follow Friday #FF’ trend on Twitter as contributing to the toxicity. While, on the surface, it’s a benign and even celebratory ritual, Bluman argues that it’s actually dangerous. “Do you know the person you’re recommending?
Do you have a right to condone? Are you taking accountability for whom you’re recommending?”
Influencer lists garner similar criticism, but from multiple sources. “Clickbait lists worry me because journalists might turn to these lists, erroneously ascribing expertise and elevating popular voices over true subject matter experts,” says Moussouris.
“I don’t see any use for influencer lists,” agrees Graham Cluley, host of the Smashing Security podcast. “When I see my name on one, I get the impression the company who wrote the list wants me to share it with my audience in an attempt to gain more followers or readers themselves. I think it’s important that people who don’t regularly appear on awards lists are recognized for their achievements rather than the same old tired names appearing over and over again.”

Influencer lists are damaging because they are not based on skill, testimonials or proof. They too are based purely on follower counts,” mulls Forte. “I’m really disappointed in this aspect of the industry. Celebrating achievements should require evidence of achievement.”
Follow Friday and influencer lists often result in an echo chamber in the industry, with the same names popping up time again and often based on nothing more than an algorithm around social reach – a pillar that should not be held up as something to aspire to.
Does the information security community buy-in to all this ‘celeb’ adoration, coddling, worship? Not often, according to Cluley. “In my experience, many people who work in infosecurity have a healthy skepticism and lean away from those who have reached a level of notoriety unless they prove themselves not to be arseholes.”
“I want every girl in the world to pick up a guitar and start screaming” – Courtney Love
It’s important to consider that for minorities in the industry, recognition or status is harder to come by. Therefore, a platform to promote their work and amplify their voice is less about indulging a desire for fame and more about necessity. Alyssa Miller, hacker, researcher and security advocate, notes that “underrepresented individuals rarely receive the credit for their accomplishments in parity with how white cis-gendered men are recognized.” She argues that women, BIPOC, Latina/Latino and the LGBTQ+ community have all “been forced to be more self-promotional in order to have their work seen and celebrated.”
Moussouris agrees. “Women have to work twice as hard to be considered half as good, but that’s been true of underrepresented groups forever,” she says. “Women and people of color are treated with disrespect and suspicion of their motives in their online posting, versus the reaction to white males doing shameless self-promotion that seems accepted without pause.”
Miller doesn’t consider herself an infosec rock star but instead refers to herself as “one of the high follower-count security people.” She says: “Ultimately, I wish the whole idea of infosec rock star would just go away; it’s not healthy. Katie Moussouris said it best on Twitter when she stated, ‘I want friends, not fans.’ I can’t think of a more simple yet effective way of communicating how I and other high follower-count security people feel about the whole rock star culture.”
“I won’t be a rock star, I will be a legend” – Freddie Mercury
It’s easy to get people talking about what doesn’t make an ‘infosec celeb.’ To conclude on that front, it’s follower count, the desire or drive to be ‘famous,’ and shouting loud and causing controversy just to build an audience.
Some interviewed for this feature stood firm that ‘infosec celebs’ are entirely fictional. The most popular opinion, however, is that true ‘infosec celebs’ are rare but they all have something in common: a genuine contribution to the industry. Javvad Malik, lead security awareness advocate at KnowBe4, puts it like this: “the real rock stars, in my opinion, are the ones that help the most people get more secure, and help inspire the next generation or current generation even, to enter and thrive in the field.”
Cluley has a similar perspective. “If we’re going to use the phrase at all, I’d like it to be used to describe those who encourage others in the industry, call out bad practices where they see them and act with humility.”
Forte again points to a genuine contribution. “The only candidates worthy of the title infosec rock star have created things that make the industry safer, better and more capable. True infosec legends, I’d rather call them that, have created things, built businesses or tools, told poignant stories of past wrongdoings and most crucially, all have substance behind them.”
For Moussouris, it’s even simpler than that. “Kindness,” she answers, “nothing else matters.”
“Rock stars did not invent burning out. They just do it louder” – Rob Sheffield
Although many strive to see their name in cybersecurity lights, so to speak, some that have achieved said fame note a dark side. For Jack Daniel, it’s the pressure to “always be on.” He explains that with a face (or perhaps a beard) as well known as his, there’s serious pressure, every time he attends an event or is in public, to be switched on. This, he describes, can be exhausting.
Moussouris explains, how she is sometimes seen as “just an influencer” instead of a person of substance in the field she so loves. It’s ludicrous to imagine that someone who has given so much to an industry could be so wrongly and disrespectfully labeled.
Also worth consideration is the trolling that can result from a high follower count. Forte has spoken publicly about her experience. “As my follower count grew, so did the trolling, abuse, threats, upset, torment and depression.” In fact, she declares those negative consequences the only consequences of her rapid increase in followers. “I never got more money, success or respect from my follower count. It doesn’t yield anything positive or tangible,” she concedes.
“The only thing worse than a rock star is a rock star with a conscience” – Bono
Research for this feature unveiled it as a highly emotive topic, with many feeling passionately about the subject. General consensus serves the fable that the pursuit of notoriety is not the same as the pursuit of excellence, and while the latter is admirable, the former is foolish.
Fame, for fame’s sake, is a shallow goal and one that most likely will lead to both disappointment and emptiness.
While some view the concept of infosec fame with utter disdain, others are more receptive to it, although the latter category stipulates that such status must be earned through exceptional contribution, not a large following.
Alyssa Miller serves up a sliver of reality with the intelligent reflection that “even the most notable among us are largely unknown in mainstream society. It’s a unique perspective that social media allows us to forget.”
In the music industry, the greatest rock stars boost up-and-coming artists. It would be wonderful to see infosec ‘rock stars’ – or whatever you choose to call the industry’s brightest and most recognized talent – doing the same. “Share the stage, share the spotlight, promote and defer to others when appropriate,” advises Jack Daniel.
The final word goes to Moussouris, a professional who surely deserves the ‘infosec rock star’ title if it’s ever deemed appropriate. “The most punk rock thing to do is to smash the guitar and kick the amp over at the end of the set. So far, none of us have burned the internet down, so until then, there are no true infosec rock stars!”
*Drop the Mic*
Name Dropping with Javvad Malik
Dozens of people were quick to send in suggestions of people they consider ‘infosec rock stars,’ but Javvad Malik shared a well-considered round-up of those he deems worthy of a star on the (hypothetical) infosec ‘walk of fame’ and categorizes them as follows:
General Rock Stars
“Jack Daniel comes to mind, not least because of his ZZ top beard, but because he literally created most of what we call the ‘community.’ There's Wendy Nather, Brian Honan, Troy Hunt, Bruce Schneier also in this category.”
Vendor Rock Stars
“There are rock star types from the vendor side of the industry who have built great companies that have impacted security in positive ways. The late John McAfee (for all his flaws), Dr Solomon, Dug Song, Kaspersky, Dell, Haroon Meer, etc.”
Offensive Rock Stars
“Then there are the security people who have legally – and sometimes illegally – broken stuff, and it's gotten them fame or recognition beyond the security world. There's the old school people like Kevin Mitnick, or people like Charlie Miller (car hacking), or Ken Munroe (hacks any smart thing) and other names that are slipping my mind right now.”
Educator Rock Stars
“There are the educators like the late Shon Harris, or Vivek Ramachandran (security tube), etc., and then Katie Moussouris who basically created the whole bug bounty world.”
Your Name’s On the List: Infosec's 'Walk of Fame'
The names commonly put forward as candidates for the infosec ‘walk of fame’ from the contributors to this article:
- Jack Daniel
- Rik Ferguson
- Brian Honan
- Troy Hunt
- Mikko Hypponen
- Dan Kaminsky
- Dave Kennedy
- Brian Krebs
- John McAfee
- Alyssa Miller
- Charlie Miller
- Katie Moussouris
- Wendy Nather
- Bruce Schneier
- Richard Thieme
