There has been a 44% increase in cyber-attacks exploiting public-facing applications, IBM X-Force has warned.
The newly published the 2026 IBM X-Force Threat Intelligence Index report points to missing authentication controls and AI-enabled vulnerability scanning as major drivers behind the spike.
Vulnerability exploitation emerged as the leading cause of incidents in 2025, accounting for 40% of cases observed by IBM X-Force. At the same time, active ransomware and extortion groups grew 49% year over year, signalling a more fragmented ecosystem. Publicly disclosed victim counts rose by roughly 12%.
"Attackers aren't reinventing playbooks, they're speeding them up with AI," said Mark Hughes, global managing partner for cybersecurity services at IBM. "The core issue is the same: businesses are overwhelmed by software vulnerabilities. The difference now is speed."
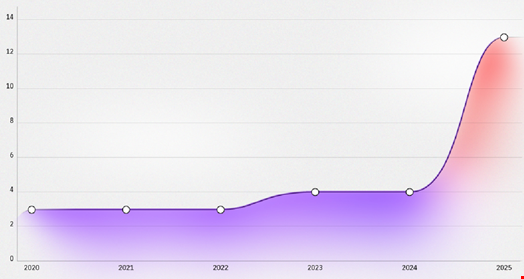
IBM found that large supply chain and third-party compromises have nearly quadrupled since 2020. Attackers are increasingly targeting software build and deployment environments, along with SaaS integrations, exploiting trusted relationships and CI/CD automation in development workflows.
The report attributed part of this growth to the blurring line between nation-state and financially motivated threat actors, as tactics circulate on underground forums and AI streamlines reconnaissance and exploitation.
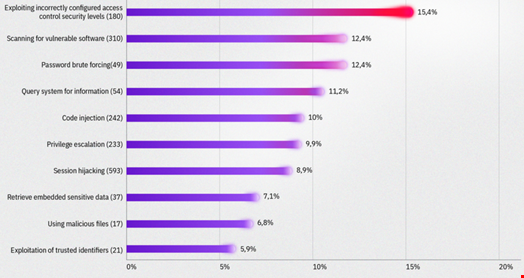
Additional findings from the report include:
-
Infostealer malware exposed over 300,000 ChatGPT credentials in 2025
-
Manufacturing accounted for 27.7% of incidents, marking its fifth consecutive year as the most targeted sector
-
North America represented 29% of observed cases, up from 24% in 2024, becoming the most attacked region for the first time in 6 years
AI Lowers Barriers And Expands Risk
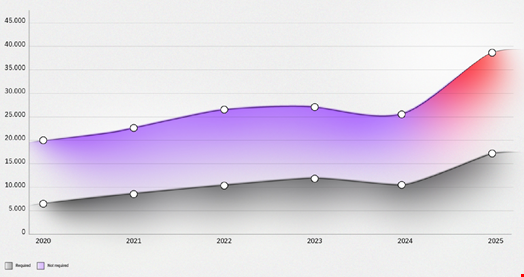
The research also describes how leaked tooling and AI capabilities are lowering barriers to entry for ransomware actors.
Smaller, transient groups are reusing established playbooks and automating parts of their operations. As multimodal AI models mature, IBM expects adversaries to automate more complex tasks, including reconnaissance and advanced ransomware attacks.
AI is also accelerating the attacker lifecycle more broadly. IBM observed threat actors using AI to conduct research, analyse large data sets and refine attack paths in real time. In one example, North Korean IT worker schemes employed AI-driven image manipulation to create synthetic identities and translation tools to engage across global marketplaces.
The findings suggest that while techniques may be familiar, the pace and scale of exploitation are shifting rapidly as AI becomes embedded in the cybercrime ecosystem.
