Speaking at Infosecurity ISACA North America Expo and Conference in New York, Tony Rock, chief operating officer at Lockpath, discussed the challenges many security departments face in building a business case to communicate their risk management and security programs.
“Our [infosec pros] jobs are hard, when you think about the world that we live in: no resources, changing priorities, no funding, compliance [etc.],” Rock said.
“We need to find a way to communicate the issues we are having within the organization and how we can use those to minimize risk and deliver value.”
Fundamentally, security leaders can become frustrated, Rock admitted, “but at the same time, our business executives are frustrated too, ” and they do not view or understand security and risk in the same way as security professionals.
Security leaders must understand the business use cases of security strategies to drive more value, he added. “Not being able to communicate effectively is a significant problem, and at the end of the day, the people on the business side control the check books, but they normally don’t quite understand what we do and how we deliver value.”
It’s therefore down to security leaders to align and articulate their needs with the needs of the wider business stakeholders, including:
- Linking needs to performance metrics
- Funding business cases
- Reporting status for action
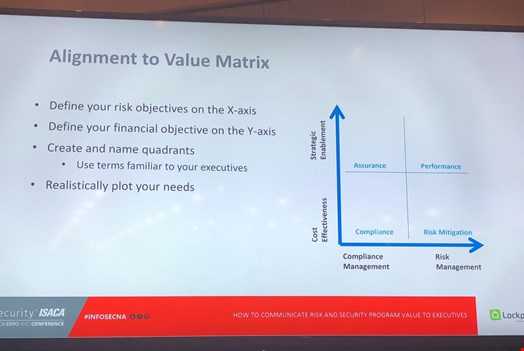
Security leaders must understand the cost and benefit of their objectives, and frame reporting of results or requests for resources in the context of business executives, Rock continued. He then shared an ‘alignment to value’ diagram (below) that can aid security leaders in achieving this.
“At the end of the day, there are business benefits to [doing] this, because this is what essentially allows us to fund the things that we need to deliver to the organization.”
