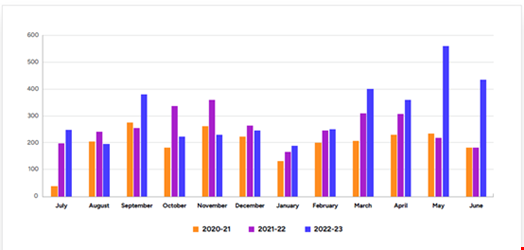
The number of victims named on ransomware leak sites reached “unprecedented levels” in the four months from March to June 2023, according to Secureworks’ 2023 State of the Threat report.
At current levels, 2023 is on course to be the biggest year on record for victim naming on so-called ‘name and shame’ sites since this practice began in 2019. It is expected the 10,000th victim name was posted to leak sites in late summer 2023, but this has not yet been confirmed by Secureworks.
The report, which presented insights from July 2022 to June 2023, revealed that one-off mass exploitations of specific vulnerabilities was the main factor for the record numbers of named victims in the latter four months of the period:
- March – Fortra GoAnywhere, exploited by Clop
- May – Zimbra mail server, exploited by MalasLocker
- June – MOVEit Transfer, exploited by Clop
A LockBit operator, dubbed GOLD MYSTIC by Secureworks, was the most active ransomware group during the 12-month period covered, publishing nearly three-times the number of victims as the next most active group, ALPHV(BlackCat), operated by a group known as GOLD BLAZER.
Alongside known groups, Secureworks revealed that new ransomware schemes posted numerous victims from March to June 2023. This includes 8BASE listing nearly 40 victims on its leak site during June 2023.
Don Smith, VP threat intelligence, Secureworks Counter Threat Unit, noted: “While we still see familiar names as the most active threat actors, the emergence of several new and very active threat groups is fuelling a significant rise in victim and data leaks. Despite high profile takedowns and sanctions, cyber-criminals are masters of adaptation, and so the threat continues to gather pace.”
The researchers acknowledged that leak sites alone do not provide an entirely accurate picture of the state of ransomware, as they only list victims who have not paid the ransom and are not used by all ransomware groups.
Dramatic Fall in Ransomware Dwell Time
The 2023 report found that ransomware median dwell time was under 24 hours, representing a dramatic fall from 4.5 days during the previous 12 months. In 10% of cases, ransomware was deployed within five hours of initial access.
Smith believes this trend is due to improved cyber detection capabilities, with cyber-criminals speeding up their operations to reduce the chances of being stopped before deploying ransomware.
“As a result, threat actors are focusing on simpler and quicker to implement operations, rather than big, multi-site enterprise-wide encryption events that are significantly more complex. But the risk from those attacks is still high,” commented Smith.
Another factor identified for the fall in dwell times is that many threat actors now deploying ransomware are lower skilled than previous operators, with less sophisticated approaches. This is due the rise of the Ransomware-as-a-Service (RaaS) model lowering the barrier to entry.
What Are the Top Initial Access Vectors for Ransomware?
Secureworks observed that the two most common initial access vectors were scan-and-exploit (32%) and stolen credentials (32%).
Scan-and-exploit, the identification of vulnerable systems which are then compromised with a specific exploit, fell significantly as a proportion of ransomware incidents compared to the previous 12 months, when it was 52%.
The proportion of incidents that started with stolen credentials also fell from the previous 12 months, when it represented 39% of ransomware intrusions.
Commodity malware delivered via phishing emails was the third most common initial access vector from July 2022 to June 2023, at 14%.
Most Effective Ways to Protect Against Ransomware
The researchers noted that the top three initial access vectors identified can either be prevented or detected at an early stage using a combination of the following measures:
- Prompt and regular patching. Secureworks said CISA and partner agencies list the top vulnerabilities that threat actors scan for, many of which contain older flaws. Organizations should look to prioritize the patching of these vulnerabilities.
- Multi-factor authentication (MFA). While the report acknowledged that threat actors are employing a variety of tactics to bypass MFA, these controls will usually prevent the adversary from advancing when weak credentials are exploited.
- Comprehensive implementing of monitoring solutions. The time lapse between data theft and use during ransomware incidents means there is enormous value for organizations in monitoring cybercrime forums for stolen data, according to the researchers. Secureworks also advised implementing network flow monitoring to detect and alert on large data transfers.
