Cyber-criminals have got so good at concealing their activity that employees often can’t tell if their account has been compromised.
In an email account takeover instance (ATO), attackers steal the credentials of employees and send phishing and spam campaigns from the compromised employee accounts. Most account takeover attacks will involve sending standard phishing emails from the infected account, leveraging the high reputation of the account. The more sophisticated attackers will send emails that have some context related to the sender and recipient's relationship (e.g., a supplier and a buyer).
Typically, an attacker will stay active until they get caught, or until the account owner realizes that they have been compromised.
Who is targeted by ATO? Well this can also vary greatly. Some of the attackers simply "spray and pray", sending emails to many random targets in an organization and hoping that one of them will fall for the phishing emails. Other attackers are much more sophisticated and will choose their targets carefully based on their title, such as targeting a CFO, a procurement manager, or an HR manager.
Out-of-office warning sign
Because messages are sent directly from a hijacked email account, the email system creates copies of the messages in the Sent Items folder. One of the most common tactics that attackers use is to immediately delete the emails they send from the Sent Items folder of the compromised account, so employees and IT will not notice the account has been compromised.
Fortunately, there is a way to exploit this subversion tactic, using AI as a signal to detect account takeover. At Barracuda, our researchers noticed that when an account takeover results in a mass phishing or spam campaign, the employee often gets a barrage of auto-replies, such as out-of-office messages from recipients who are away from their place of work for an extended period of time.
An AI classifier in an email security solutions can be trained to recognize the anomalous pattern where a user receives an out-of-office email that is not tied to any outbound email to the same user within the same window of time. Once the AI classifier identifies this anomalous behavior, the email security solution should alert customers, as well their IT administrators or IT service provide, that the account might have been compromised and allow them to take steps to stop the account from spreading malicious emails to other employees or external parties.
Signs of an ATO attack
Many companies send mass email messages internally and externally, and these legitimate activities can also result in a large number of auto replies. When a large number of out-of-office replies come into the inbox and a large number of files are deleted from the Sent Items folder, they are strong indicators of an ATO attack.
For example, the figure below, which is based on research conducted by the Barracuda team, displays the number of out-of-office emails received by employees in a certain company, which were received in the inbox folder without a corresponding outbound email in the Sent Items folder. The graph shows that there are clear spikes in certain time periods for specific employees.
It turns out that these spikes exactly correspond to when attackers took over specific employee accounts!
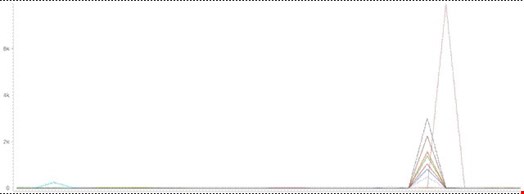
To summarize, a barrage out-of-office emails that are not tied to user-generated outbound emails are a strong signal of account takeover. An AI-based email security solution can detect these types of spikes automatically to alert on and remediate incidents of account takeover.
