New research has brought something significant to light. Passwords of the length and complexity deemed compliant by regulatory bodies are found everywhere within breached lists. Relying on compliant passwords does not protect your network. Join us as we take a deeper look into this issue and what can be done about it.
Regulatory Bodies Promoting Information Security Standards
Regulatory recommendations and standards promote best practices and legal requirements for organizations operating across various industries around the world. Cybersecurity requirements play a crucial part within these standards and guidance is given for what effective cybersecurity measures should be put in place. One key area of these standards entails how best to construct a secure password policy.
The new study looked at the requirements of the top five regulatory bodies promoting information security standards with specific password policy recommendations. These encompass minimum password length, maximum password length and password complexity.
The five regulatory bodies chosen were as follows:
- National Institute of Standards and Technology (NIST). This body defines the information security standards for federal agencies (or organizations working with those agencies) in the US.
- Health Information Trust (HITRUST) for the Health Insurance Portability and Accountability Act (HIPPA). This offers a framework to comply with standards such as ISO/IEC 27000-series and HIPAA.
- Payment Card Industry Data Security Standards (PCI DSS). This standard was created by major credit card companies – such as Visa, Mastercard, and American Express – in an effort to protect credit card data from theft.
- The Information Commissioner’s Office (ICO) for the General Data Protection Regulation (GDPR). The ICO is responsible for enforcing the GDPR, also offering non-binding password guidance that the GDPR fails to provide.
- The National Cyber Security Centre’s (NCSC) Cyber Essentials. This approved accreditation scheme outlines a baseline for cybersecurity standards. These standards are mandatory for government contracts.
An Analysis of 800 Million Passwords
Over 800 million known compromised passwords were analyzed in the research, a subset of over 2 billion passwords contained within Specops Software’s Breached Password Protection database. The passwords were compared against the password policy recommendations of each of the five standards mentioned above. The chart below shows the percentage of those compromised passwords that would otherwise fulfill the regulatory recommendations.
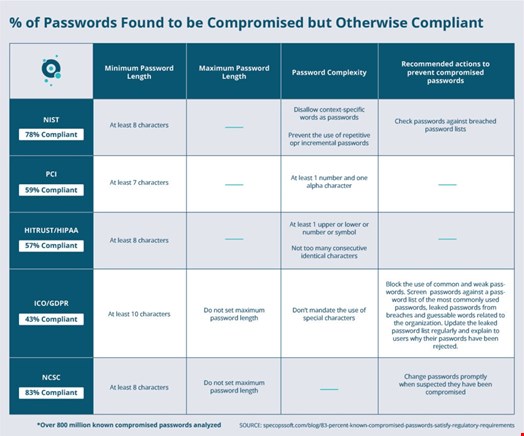
The shocking truth is that as many as 83% of the known compromised passwords would have met compliance standards.
Reassuringly, both NIST and ICO/GDPR standards include the recommendation to use a known compromised password list to prevent the use of breached passwords as an essential additional layer of security.
The ICO/GDPR delivered the most comprehensive instructions for compromise password prevention. In addition, they recommend custom dictionaries for terms related to the organization and improve the user experience by providing end-user feedback when passwords are rejected.
Overall, the analysis gives a clear message that solely relying on minimum eight-character passwords with or without complexity will do nothing to protect your network if the password exists on a breached list.
What Can You do to Protect Your Organization?
Understanding whether you are housing compromised passwords in your network is an advisable first step. If targeted by a brute-force password attack, your cyber defense could fail within seconds.
By running a password auditing tool, you can find out how many of your Active Directory users are using compromised passwords. This includes the Specops Password Auditor, a free read-only tool that scans against a list of over 1 billion compromised passwords and identifies other password vulnerabilities in a dashboard view.
Evaluate your password policies. Are you solely relying on compliance requirements? Additionally, you should aim for length over complexity – longer passwords are harder to crack. Turn on 2FA where available and consider third-party alternatives to Microsoft’s password policy tool. Features such as custom dictionaries, passphrase support, length-based aging and client feedback provide additional security, improved user experience and simplify compliance with industry regulations such as NIST or NCSC.
If you’re looking into password security in your organization and want to block breached passwords used in real-world attacks and have true fine-grained control over your password policies, request a free demo of Specops Password Policy.

