The Madagascar government likely used the Cytrox-developed Predator spyware to conduct political domestic surveillance ahead of the country’s presidential election, according to research by Sekoia.
French threat intelligence firm Sekoia’s latest technical analysis of Cytrox’s infrastructure was prompted by recent revelations that Predator had been installed on the iPhone of the former Egyptian MP Ahmed Eltantawy.
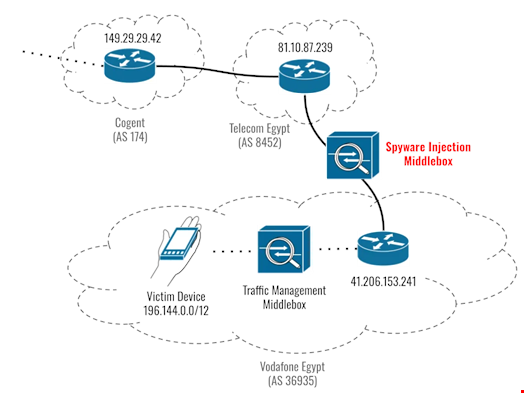
Citizen Lab, a tech research laboratory based at the University of Toronto, found that in August and September 2023, Eltantawy was targeted via network-based injection, redirecting him to malicious web pages when he visited non-HTTPS sites by exploiting a zero-day exploit chain (CVE-2023-41991, CVE-2023-41992, CVE-2023-41993) used to install Predator on iOS versions up to 16.6.1.
Cytrox is a subsidiary of Intellexa, an Israeli-founded, Greece-based surveillance company responsible for developing several spyware tools, including Predator.
Sekoia found a list of virtual private servers (VPS) linked with fake URL shorteners or malicious websites, including typosquatting news websites. These websites are likely used as entry points for exploit kits.
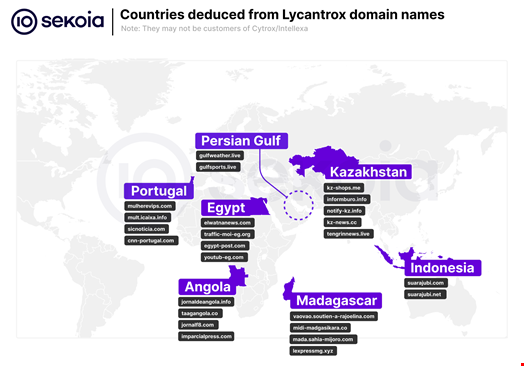
“At the end, 121 unique active domain names were found being related with high confidence to an infrastructure cluster linked to the Lycantrox intrusion set,” reads the report. Lycantrox is the name given by Sekoia when tracking Cytrox infrastructure.
Some domain names were linked with Madagascar-based websites, including WordPress blogs containing real articles taken from the Malagasy newspaper Midi Madagasikara.
Based on these findings and the alleged existence of a contract between Intellexa and Madagascar’s government for the collection and processing of interception data, previously reported by Intelligence Online, Sekoia assessed it is “plausible Madagascar government services – such as police or domestic intelligence – did purchase and leverage Cytrox’s Predator malware to conduct political domestic surveillance, months before the election.”
Read more: Why Zero Days Are Set for Highest Year on Record
Which Governments Are Linked to Predator Spyware?
In the report, Sekoia also found domain names linked with a typosquatted IP address of Jubi TV, an Indonesian opposition media in West Papua province, and Angolan media websites. The firm estimated that it was “possible” that the regimes of these two countries used Predator spyware.
Other domain names found by Sekoia researchers were located in Egypt, Portugal, Kazakhstan and the Persian Gulf.
The firm believes that these novel, previously unheard-of findings about the use of Predator could be attributed to Cytrox having recently hardened its reverse proxies.
“Sometimes, too much hardening can be discriminatory from a defender point of view, as we can see with this correlation,” the researchers wrote.
Mobile users who want to check the presence of domain names leveraged by Cytrox to deploy Predator can download the ‘MVT for analysis’ or ‘Spyguard’ apps.
Read more: NSO Group's Recent Difficulties Could Shape the Future of the Spyware Industry
