Cyber attackers continue to speed up vulnerability exploitation and last year 28.96% of known exploited vulnerabilities (KEVs) identified by VulnCheck were exploited before being publicly disclosed, or on the day they were reported.
This from cybersecurity firm VulnCheck’s State of Exploitation 2026 report, published on January 21, which shows zero-day and one-day exploitation is accelerating, up from 23.6% in 2024.
While the report considers the discoverability of a vulnerability as the day its common vulnerabilities and exposures (CVE) identifier is published, Patrick Garrity, vulnerability researcher at VulnCheck, told Infosecurity that the reality is more complex.
"Some were disclosed in public advisories first, then became exploited and a CVE was published after the facts," he explained.
This means that not all KEVs being exploited before or on the same day of CVE issuance are zero day vulnerabilities. Nevertheless, this rise from 24% to almost 30% shows that cyber threat actors continue to step up the pace by which they exploit unpatched vulnerabilities.
In 2025, VulnCheck identified 884 vulnerabilities for which evidence of exploitation was observed for the first time, a 15% increase over the previous year’s total.
Exploitation activity spanned hundreds of vendors and products. Network edge devices, including firewalls, VPNs and proxies, were the most frequently targeted technologies with 191 KEVS identified by VulnCheck in 2025. This was followed by content management systems (CMS) with 163 KEVs and open source software with 129 KEVs.
Time-to-Exploitation Patterns Remain Consistent
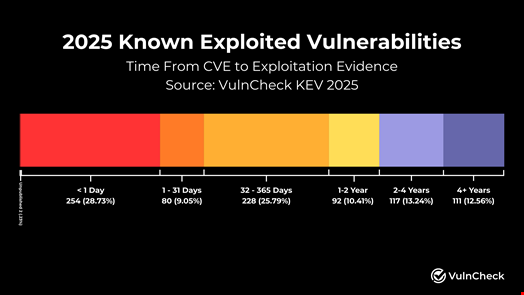
The report showed that time-to-exploitation patterns in 2025 remained highly consistent with 2024, indicating stable and sustained attacker behavior.
Operating systems (OS) were most affected by zero-day and one-day vulnerability exploits. Of the KEVs impacting OS identified by VulnCheck in 2025, almost half were exploited before or just after the vulnerabilities were publicly disclosed.
The technologies most targeted by old vulnerabilities, those disclosed more than four years before they were exploited, included developer tools, network devices and hardware.
Finally, the VulnCheck report showed that ransomware attribution continued to lag behind initial exploitation disclosure in 2025, suggesting that attribution for vulnerabilities exploited in 2025 will continue to grow as additional research is published.
Read now: Experts Welcome Global Cybersecurity Vulnerability Enumeration Launch
