Unnecessary escalations cost time, focus and confidence. Add a week of noisy alerts and MTTR starts to climb in a way that’s hard to explain in a report, and even harder to fix with “work faster” pressure.
Top CISOs are rolling out a clear action plan that tightens early decisions, reduces back-and-forth, and keeps cases moving from first signal to containment. That approach has helped cut MTTR by 21 minutes per case, without sacrificing investigation quality.
Accelerating Triage and Response with Sandbox Analysis
Reducing MTTR in a consistent way usually comes down to one thing: cutting the time spent validating alerts before action is taken. A sandbox helps teams do that by turning suspicious files and links into clear behavioral evidence early in the workflow.
Why Sandboxing is Becoming a Priority
Sandboxing has become a practical response to a simple reality: teams are expected to move faster, while early alert context is often limited. As a result, more organizations are placing sandbox execution at the start of triage to reduce delays caused by manual checking.
Early Execution of Suspicious Artifacts
The most effective change is also the simplest: make sandbox execution the default starting point for suspicious files and links that meet defined risk criteria (unknown sender, new domain, macros/scripts, unusual download chains, high-severity alerts).
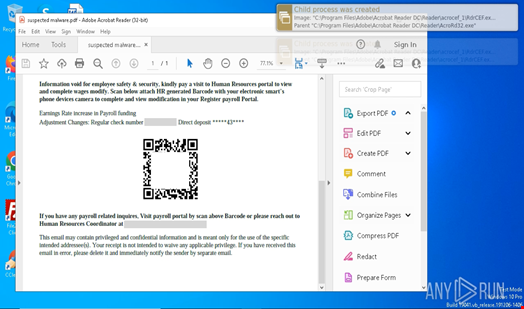
This gives the organization immediate behavioral evidence, including process activity, outbound communication, dropped files, persistence attempts, and credential-related behavior.
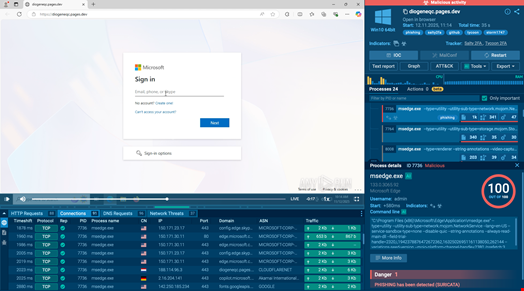
With interactive sandboxes such as ANY.RUN, this early step can produce a fast, evidence-based first verdict. ANY.RUN reports that in roughly 90% of cases, teams surface the full attack chain within about 60 seconds, turning unclear alerts into actionable evidence at the start of the investigation.
Integrate ANY.RUN to embed evidence-based triage and cut MTTR by 21 minutes per case across your SOC.
Automated Attack Chain Exposure
Many threats do not reveal their true behavior immediately. They require user interaction, staged execution, or delayed payload delivery. When this interaction is performed manually, investigations slow down and key behaviors may be missed.
Interactive sandboxes automate this process, triggering execution paths and exposing the full chain earlier in the investigation. This reduces the time spent attempting to reproduce attacker behavior and accelerates clarity on how the threat operates.
By revealing the complete chain quickly, teams reduce investigative delays and move to containment sooner.
Reducing Unnecessary Escalations
According to ANY.RUN’s reporting, organizations that operationalise sandboxing early can reduce pressure on frontline teams while improving decision quality. This shows up as up to a 20% decrease in Tier 1 workload and a 30% reduction in Tier 1 to Tier 2 escalations, as junior staff can resolve more cases with clear, behavior-based evidence.
Conclusion
Cutting MTTR starts with faster clarity. When suspicious files and links are executed early in a sandbox, teams get behavioral evidence immediately, expose the full chain faster, and reduce unnecessary escalations. That is how organizations have cut MTTR by 21 minutes per case.

Integrate ANY.RUN into your triage and response workflow to reduce MTTR, lower escalation rates, and improve investigation throughput.

