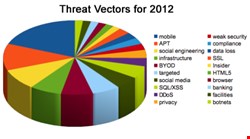
We should start with a caveat: Many of these threats should be combined. For example, social engineering threats will often be focused on social media; the ‘bring your own device’ (BYOD) threat is closely linked to the mobile threat; infrastructure attacks will likely use APTs, and so on. Nevertheless, the overall picture is a pretty good overview of the evolving threat landscape for 2012.
1: Mobile Malware
Not surprisingly, given the exponential growth in mobile malware over the last few months, the mobile vector is seen as the biggest threat. “In 2012 we will start to see a major threat emerging as companies start to roll out bring your own device and iPad initiatives,” warns Blue Coat Systems. “The big attack vector in 2012 is mobile – Android based devices, tablets, ipads, smart phones – both in delivering payloads and being attacked themselves,” comments Guidance Software. “Whether it’s surfing the web, social networking, gaming, or email, mobile malware has a growing number of possible infection vectors that will most certainly make their way out of the ‘proof of concept’ realm and more into the mainstream,” says AppRiver.
Mobile devices are “the soft under belly that hackers will find irresistible,” warns Vigil software. “Anti-malware for smartphones and tablet devices is in its infancy,” explains M86 Security, “and cybercriminals will continue to target these devices.”
“Attacks will be simple and straightforward as there aren’t many defense mechanisms to block them,” adds Trusteer. Furthermore, warns the Information Security Forum, “many of the web applications used on these devices are unlikely to have undergone formal software development and testing.”
2: The APT
The advanced persistent threat (APT) is the second most predicted threat. Threats to national infrastructures (coming in fourth) and some targeted attacks are also likely to involve APTs. A key perception is that APTs will increasingly be used against nations and corporations rather than individuals. The current year “has seen the APT gain more awareness and there are indications that the hacking community is using such mechanisms as Duqu to gain access to target systems as opposed to users,” explains Cyber-Ark.
APT attacks “against high-profile companies and government agencies in 2011 will become even more predominant in 2012,” warns Lancope. A “key threat for 2012,” adds BAE Systems Detica, “is most likely to be an increase in economic cyber espionage. As a result we predict that protection against advanced persistent threats (APT) will rise up the corporate agenda and move to centre stage.”
3: Social Engineering
Social engineering is seen as the third most dangerous threat vector. This should be considered in conjunction with the social media threat and spear phishing, since the intelligence for social engineering will often come from the social networks of the target. We predict, says Tripwire, that “the biggest infosec threats in 2012 will come from attack vectors that rely on social engineering. We've seen a rise in spearfishing attacks and other targeted attacks in the last couple of years, and the relative success of these attacks makes it reasonable to assume we'll see more of them.” RandomStorm agrees. “Social engineering will continue to pose a huge threat to private records in the public sector and financial data and IP in the private sector,” it warns. “This is because humans are naturally trusting and so they will always be the weakest link when it comes to physical and online security.”
Infrastructure Threats
Threats to the national infrastructures are also increasing. “Nation states’ critical national infrastructures will increasingly face cyber attacks,” warns LogRhythm, “with world economic and political instability precipitating greater activity in this area.”
Kaspersky sees the targeted attack, whether it’s APTs or spear phishing aimed at the individual, corporation or national infrastructure, as the biggest threat. “Targeted attacks against organizations and government bodies, continuing the trend we have seen in 2011,” it says. “The main objective is financial gain,” but also adds Kaspersky, to disrupt and damage a competitor or infrastructure.
“SQL and XSS vulnerabilities will be the fastest growing threat of 2012,” believes Outpost24, “a trend continuing from the raft of data breaches seen in 2011. This is down to the relative ease with which hackers can scan for such flaws in the coding of websites and exploit them. SQL and XSS attacks are simple and devastatingly effective.”
DDoS Attacks
DDoS attacks are almost always delivered via botnets, so the two should be considered together. DDoS is the number one threat predicted by IBM’s X-Force. “We expect to see more of the sort of politically motivated hacktivism that dominated the headlines in 2011,” it suggests. “It’s particularly important for organizations to develop a DDOS response strategy in advance so that they know exactly what to do when that dreaded day comes.”
SSL, says Imperva. “Attackers are exploiting vulnerabilities in the various implementations of the SSL protocol. Furthermore, we are seeing a rise in attacks which target the worldwide infrastructure that supports SSL. We expect these attacks to reach a tipping point in 2012.”
Ravenswood Consultants sees a growing threat to compliance from the increasing use of the cloud. It cites the problems of insecure access and potential foreign storage as problems. “Both of these instances are likely be in breach of the EU directive on personal data security, encoded in the UK as the Data Protection Act, 1998.”
Privacy
And finally, continuing the theme of personal data, ESET’s David Harley considers privacy to be a primary threat vector. This will be the outcome of increasing international attempts to bolster security by sharing information. “That may not sound like a threat,” he says, “but do you trust your government to make only ‘appropriate’ use of your data, and to keep that data secure?”
Finally...
One last comment. Despite all the threats and warnings and predictions you’ll come across over the next month, remember this: it will be the threat that you didn’t expect that gets you.