An undocumented malware implant suspected to be associated with a China-linked actor has been identified by researchers at Cato Networks’ Cyber Threats Research Lab (CTRL).
Their discovery was made when they responded to an intrusion attempt affecting the Indian branch of an unnamed global manufacturing customer with multiple regional sites in April 2026.
While the Cato CTRL team managed to block the intrusion, they also identified suspicious traffic associated with a third-party user connected to the customer environment.
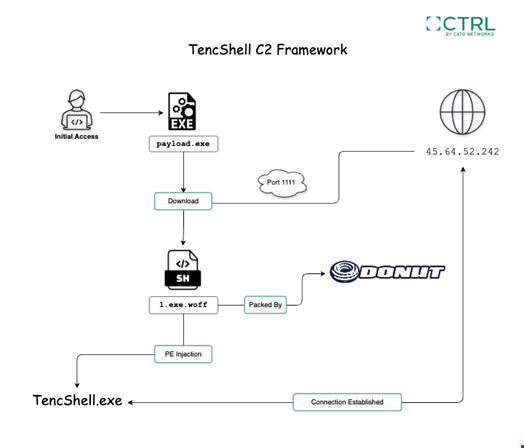
The attack chain used a first-stage dropper, Donut shellcode, a masqueraded .woff web-font resource, memory injection and web-like command-and-control (C2) communication.
The operation aimed to infect the target with a customized Go-based implant derived from the open-source Rshell C2 framework.
Designed for cross-platform offensive security use, the original Rshell framework includes remote command execution, file and process management, terminal access, in-memory payload execution, multiple C2 transports and a model context protocol (MCP) server, used notably for AI agent communications and operations.
The version observed is an undocumented variant of Rshell, customized and repackaged for this operation, with “communication and delivery changes that made it more suitable for the attacker’s campaign,” explained the researchers in a May 13 report in which they shared technical details about the campaign.
Cato CTRL named the implant ‘TencShell’ because it combines shell-style remote-control capabilities with C2 communication that imitates Tencent-like web service paths.
Based on the apparent Rshell lineage, Tencent-themed API impersonation and infrastructure patterns, Cato CTRL suspect the threat actor behind this operation to be based in China or linked to Chinese-backed hacking groups. However, they noted that the evidence is “not sufficient on its own” for attribution.
If successful, TencShell could have granted the attacker comprehensive access to the target environment, including remote command execution, in-memory payload execution, proxying, pivoting, system profiling and a path to deploy additional tooling.
This operation shows that many attackers can now rely on adaptable open source tooling to conduct sophisticated intrusions and often no longer need custom malware development pipelines.
“Rather than building a completely new malware family, the attacker adapted available offensive tooling and attempted to blend the activity into normal enterprise traffic,” noted the researchers.
