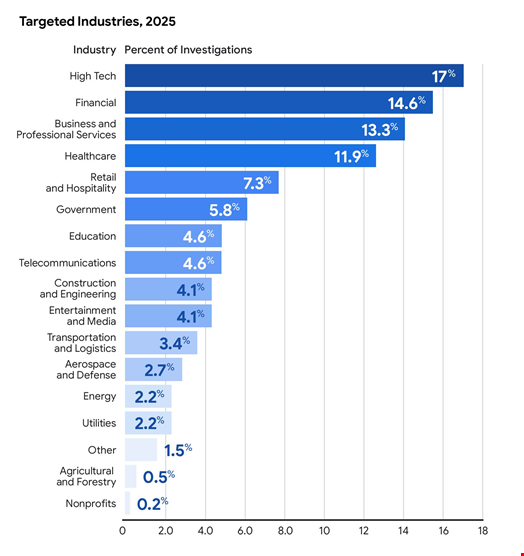
The high-tech sector was the most targeted industry for cyber-attacks in 2025, dethroning financial services as the primary focus of threat actors, according to Mandiant’s latest incident response data.
High tech companies accounted for 17% of all Mandiant investigations in 2025, the Google Cloud-owned firm noted in the M-Trends 2026 Report, published on March 23.
In comparison, finance, which led in 2023 and 2024, represented 14.6% of Mandiant investigations over the past year. Business and professional services and healthcare were also heavily targeted, making up 13.3% and 11.9% of all investigations, respectively.
Dwell Time Rises from 11 to 14 Days
In 2025, Mandiant and Google Threat Intelligence Group (GTIG) identified 83 malicious cyber campaigns – focused efforts by one or more threat groups pursuing a single objective – and eight global cyber events – when multiple groups using similar tactics, such as exploiting a new vulnerability.
These cyber events affected organizations across 73 countries.
Out of the 91 incidents, Mandiant investigated 35 campaigns and six global events.
Based on these investigations, Mandiant observed that that the global median dwell time rose from 11 days in 2024 to 14 days in 2025.
Dwell time is calculated as the number of days an attacker is present in a compromised environment before they are detected.
This increase was largely driven by North Korean-linked cyber espionage campaigns and IT worker incidents which both had median dwell times of 122 days, said Mandiant researchers.
Watch now: Inside North Korea's IT Worker Scam - Sophos CISO Shares How to Stay Protected
Global ClickFix Adoption
One of the most active global events was the growing adoption of the ClickFix social engineering technique.
ClickFix involves attackers using a prompt, typically on a phishing page, to convince users to execute PowerShell or other system-level commands under the guise of fixing problems or verifying their legitimacy.
In 2025, Mandiant and GTIG identified dozens of threat clusters incorporating this technique, particularly threat clusters focused on widespread initial access operations.
“Variants of the technique observed in 2025 used a variety of lures, including CAPTCHAs, verifications for video conference and meeting invitations, driver or operating system updates, and enterprise software compliance verification,” said the report.
Read more: What is ClickFix and How to Prevent It
Mandiant Tracks 661 New Threat Clusters and 714 New Malware Families
GTIG and Mandiant began tracking 661 new threat clusters and 714 new malware families in 2025, bringing the total number of tracked threat clusters to more than 5000 and of tracked malware families to more than 6000.
In 2025 investigations, Mandiant encountered 288 threat groups, 205 of which were newly tracked. Both numbers are lower than those observed in 2024.
However, the researchers identified 224 malware families used in investigated campaigns, compared to 205 in 2024.
Those 224 strains include 126 newly tracked families and an additional 98 malware families that were first discovered in prior years.
Initial Access: Exploits Lead, Vishing Surges
Vulnerability exploits represented the most frequently observed initial infection vector for the sixth-year running, comprising 32% of Mandiant investigations in 2025 in which an initial infection vector could be identified.
Meanwhile, voice phishing (vishing) surged to become the second most common initial infection vector (11%), reflecting a shift toward more interactive, human-led attacks.
Email phishing continued its decline, falling from 22% of initial access vectors in Mandiant investigations in 2022 to 6% in 2025.
Additionally, in 2025, most cyber threat actors continued abusing native functionalities in on-premises and cloud environments as well as legitimate tools to reduce opportunities for detection.
Mandiant reported that ransomware operators have shifted their primary objective from data theft to deliberate recovery denial, systematically targeting backup infrastructure, identity services and virtualization management planes.
Read now: Why Ransomware Remains One of Cybersecurity’s Most Persistent and Costly Threats
