The team behind the US National Vulnerability Database (NVD) can’t keep up with the explosion of new reported vulnerabilities, said a top official of the US National Institute of Standards and Technology (NIST), which hosts the database.
Speaking at VulnCon26's in Scottsdale, Arizona, on April 15, Harold Booth, a NIST computer scientist, said the NVD had to make operational adjustments in how its data analyst enrich vulnerabilities to address the “record growth” of reported common vulnerabilities and exposures (CVEs).
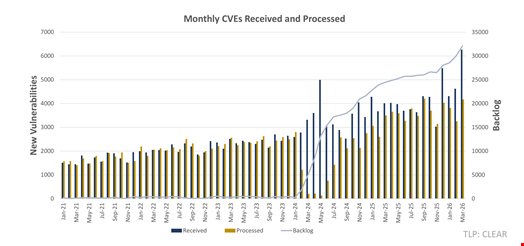
“CVE reporting keeps increasing – and trust me, at the NVD, we see them all – and our ability to keep up is just not there, so our backlog keeps increasing too,” Booth said.
The data analyst will thus shift to a risk-based approach that will guide how they prioritize which CVE to process and enrich first.
This new approach implies bold moves, including the NVD dropping routine enrichment for all currently unenriched vulnerabilities reported before March 1, 2026.
Additionally, the NVD will prioritize enriching vulnerabilities found in software used by the US federal government or in critical software as defined by the Executive Order 14028, published in 2021.
The NVD will also give precedence to vulnerabilities included in the US Cybersecurity and Infrastructure Agency’s (CISA) Known Exploited Vulnerabilities (KEV) list.
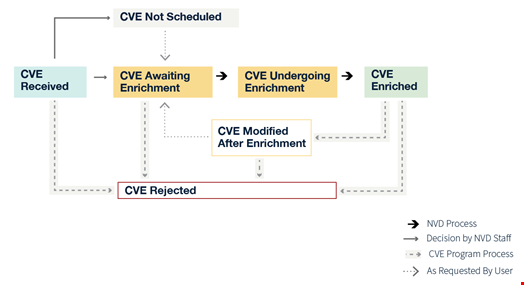
“All submitted CVEs will still be added to the NVD. However, those that do not meet the criteria above will be categorized as ‘Not Scheduled,’” said Booth.
“Vulnerabilities are a way for an attacker to gain access to a system that they should not and we want to close those holes as quickly, efficiently and effectively as possible. We want to focus on the ones that are important, not the ones that are unimportant,” he added.
Users can request enrichment of any unscheduled CVEs by emailing the NVD at nvd@nist.gov.
The CVE Surge Threatens NVD Capacity
This change is driven by a surge in CVE submissions, which has increased by 263% between 2020 and 2025, according to a NIST statement published on April 15.
Booth said the NVD is “working faster than ever” and enriched nearly 42,000 CVEs in 2025, 45% more than any prior year. However, they cannot catch up with the speed at which CVE’s get reported.
“Submissions during the first three months of 2026 are nearly one-third higher than the same period last year. We’ve been trying to develop new tools to help with this, but with our current methods, I will admit this is just something we can’t keep up with,” Booth said during VulnCon.
This is trend is likely to accelerate. In February 2026, the Forum of Incident Response and Security Teams (FIRST) forecast a record-breaking 50,000 additional CVEs to be reported in 2026.
Jerry Gamblin, principal engineer at Cisco Threat Detection & Response, expects an even bigger growth, with a forecast of 70,135 CVEs by the end of this year. This would reflect a 45.6% growth rate compared to 48,171 in 2025.
These forecasts do not consider recent announcements by Anthropic and OpenAI of new generative AI models – namely Claude Mythos and GPT-5.4-Cyber – that promise to autonomously find and fix cybersecurity vulnerabilities at scale.
Booth acknowledged that his team also faced a growth in the number of Common Platform Enumeration (CPE) identifiers largely due to new vulnerability discovery tools based on large language models (LLMs).
CPE is a standardized naming scheme used to uniquely identify hardware, operating systems and software applications.
New Rules for CVE Scoring and Analysis
Booth also revealed other changes in how the NVD will now enrich CVEs, following the same risk-based approach.
The NVD will no longer provide its own severity scores (CVSS) for CVEs already scored by the submitting authority, unless they deem the score doesn’t align with the vulnerability.
Additionally, the NVD will only reanalyze modified CVEs if changes materially impact enrichment data.
Users can request a score change or a new CVE analysis by contacting the NVD, which will review the submission and decide how to process on a case-by-case basis.
Finally, Booth also announced updated status labels for CVEs to “make them clearer.” For instance, the NVD will drop the previous ‘Deferred’ status and replace it with ‘Not scheduled’ to indicate the NVD will not enrich the corresponding CVE.
The NVD has published a document explaining CVE and NVD status labels, what they mean and how they compare.