Recent reports have highlighted how cyber-criminal groups are now targeting IT and incident response teams to get access to corporate networks and data. The aim of every malicious outsider is to become a privileged insider, so it’s no surprise that these kinds of individuals are in their sights. But could it be that the way that we manage system administrator and other elevated privileges is actually leaving organisations open to attack? A number of weaknesses spring to mind.
Let’s look at how reliant IT departments have become on directory services. These have traditionally been the way to control access and manage users of network infrastructure. These systems make it easy to grant access and permissions to systems but make it very hard to see what permissions a user has and how they’re using them. The nature of administrators and IT pros is that their requirements for remote access to infrastructure changes depending on the task or project they’re working on.
It’s extremely difficult to use directory services to manage these changes. As a recent survey of IT professionals revealed, half of respondents would find it difficult to identify whether an ex-employee or ex-contractor still had access. This should be a startling finding for those organisations who might be considering cyber insurance of some sort because I can’t think of a single policy that will pay out in the event of a data breach without a user access audit trail.
Which brings me to another common misconception: the risk comes from the account not the users. IT infrastructure is more organic than we think. Many networks have grown over time and legacy IT systems focused on “business as usual” perhaps don’t get the security that they should.
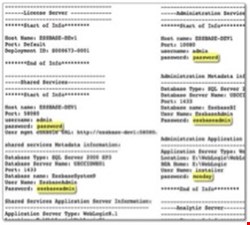
Very often shared accounts are still being used for administrative access to these kinds of servers and devices. These shared accounts are problematic for a number of reasons. In the event of a user leaving or their access being revoked, changes to the credentials have to be communicated to every else who uses them. If the credentials are rarely used, this increases the chances of passwords being stored insecurely or written down. This was exactly the case with Sony Pictures, where unprotected text files full of user names and passwords were saved on the network. Shared accounts also mean in the event of the worst happening and an organisation suffering a data breach, it would be almost impossible to track if an individual insider was responsible as a shared account would keep them anonymous.
Finally, the access model that most organisations adhere to is not one of “least privilege.”
If the description of directory services and shared accounts sounds familiar to you, it’s easy to appreciate how we end up in a situation where too many users have access to too many systems with too little visibility of their activity.
As the amount of IT infrastructure grows, boosted by virtualisation and cloud computing, we must move towards a “least privilege” model, meaning that users should only have access to the resources they absolutely need.
This is only really possible by automating requests for privileged access as much as possible. Solutions that allow for one time remote access sessions or access for a limited time that is automatically removed can go a long way to begin to address some of these security concerns. For servers that house or process particularly sensitive data, businesses should also consider monitoring and recording sessions opened by privileged users.
If there is one good thing to come from the string of high-profile data breaches involving misused elevated privileges, it’s that organisations are beginning to look for answers. After all, it’s not an issue that will just go away. The number of individuals who will require elevated privileges to network servers will only increase, organisations will continue to employ IT contractors whose access will need to be granted (and then, when appropriate, revoked) and staff will turn over or move from project to project. We’re now at a point where we must apply the same security methodology to securing access by internal users as we do in dealing with external threats from hackers and malware.
