Rainbow tables have long been part of the password cracking playbook. These precomputed lookup tables map hashes back to their original plaintext values. Instead of brute forcing a password from scratch, an attacker can use these “cheat sheets” to reverse unsalted hashes far more efficiently.
Mandiant’s early 2026 release served as the final nail in the coffin for NTLMv1. By publishing 8.6TB of rainbow tables, Google’s cybersecurity subsidiary essentially "open-sourced" the ability to bypass this legacy protocol. Their goal was transparent: to prove that NTLMv1 is no longer a hurdle for even the most basic attacker.
To understand what this release really means, organizations need to look at how attackers have traditionally used rainbow tables, what it takes to make them effective, and how today’s cracking techniques have evolved beyond them.
How Attackers Use (and Ignore) Rainbow Tables
Attackers use rainbow tables by taking a known hashing algorithm, precomputing large numbers of possible passwords and their corresponding hashes, and storing the results. When they obtain a target hash, they can look it up rather than compute it from scratch.
However, this only works under specific conditions. Rainbow tables have historically been associated with legacy protocols like NTLMv1, which lack salting, allowing identical passwords to produce identical hashes.
Even then, the hardware available today means rainbow tables are just one option. Cracking NTLMv1, for example, involves reducing the hash into its underlying DES components, a construction that’s significantly weaker than modern algorithms like SHA-256.
With hardware like an Nvidia RTX 5090, attackers can brute force those components quickly enough that precomputation becomes a convenience, not a requirement.
Are Rainbow Tables Still Relevant?
In most real-world scenarios, not really. Attackers don’t need to precompute huge tables of potential password hashes anymore. Infostealers have made it easy to gather huge numbers of passwords to use in attacks.
If a password has already appeared in a previous breach, an attacker doesn’t need to reverse a hash; they can just check if it matches something they already know. That’s why it’s crucial that organizations maintain updated breached password lists to catch compromised credentials. It’s here that specialized solutions like Specops Password Policy help.
Its Breached Password Protection feature continuously screens credentials against a database of more than 5.8 billion known breached passwords, blocking known-exposed values and reducing the likelihood of reuse.
Specops Password Policy then helps with ongoing Active Directory (AD) management by helping users create strong, memorable passwords that are more resilient against cracking attacks.
How Attackers Really Crack Passwords in 2026
Infostealers are the new shortcut to cracking passwords, but in instances where an attacker cannot simply steal a plaintext password directly from a victim’s computer, they still want flexibility and raw computer power. Attackers do not want to be tied to large, static datasets, instead of favoring approaches that adapt to whatever they find.
Today, password cracking typically centers around high-performance GPUs that process billions of hash operations per second against weaker algorithms, making real-time cracking viable without precomputation. This power is further augmented through dedicated cracking rigs that combine multiple GPUs to scale performance far beyond what rainbow tables achieve.
Rather than attempting exhaustive coverage, attackers prioritize targeted wordlists drawn from breaches, industry terms, or organization-specific context. These efforts are supported by probabilistic models like Markov-based generators that predict likely password structures to improve success rates without needing massive datasets.
Finally, AI-driven rule mutations use machine learning and advanced rule engines to refine guesses dynamically, adapting based on partial successes and common user behaviors.
These approaches share the common advantage of being portable and adaptable. They work across different hash types, do not depend on a single algorithm, and can be spun up quickly on rented cloud infrastructure.
By comparison, rainbow tables are rigid. They are built for specific algorithms and configurations, and outside of those narrow use cases, they offer little value. In environments where attackers need to move quickly and handle a mix of authentication schemes, that lack of flexibility becomes a real limitation.
Defending Against the Real Credential Threats in 2026
To reduce the risk from the techniques above, organizations should prioritize these five key defenses:
- Retire NTLMv1: Move fully to Kerberos, or at the very least enforce NTLMv2. Legacy protocols shouldn’t still be in play.
- Modernize storage: Store credentials with slow, salted hashing algorithms designed to resist cracking, not fast legacy functions.
- Encourage longer passwords: Shift away from short, complex passwords towards longer passphrases that are harder to guess and reuse.
- Check passwords against breach data: Screen new and existing credentials against known leaks to stop compromised passwords being used in the first place.
- Add phishing-resistant multi-factor authentication (MFA): Make sure a single stolen password isn’t enough. Strong MFA adds a critical layer that attackers can’t easily bypass.
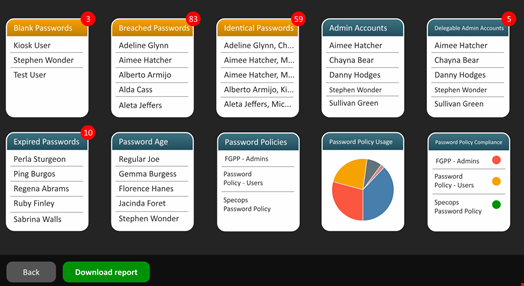
However, these controls rely on one critical capability: knowing which credentials are already weak, reused, or exposed. Most organizations don’t have clear visibility into weak, reused, or already compromised credentials across AD.
The first step toward securing your environment is a comprehensive password audit. Tools like Specops Password Auditor evaluates the state of your AD and provides an easy-to-understand report on password-related vulnerabilities. This helps your team close security gaps before attackers can find them.
If you’re interested in seeing how Specops can help defend your organization against the latest credential-based attacks, contact us today.

