A team of hackers associated to the North Korean-linked Lazarus Group has conducted a large-scale cyber theft campaign targeting over 100 cryptocurrency organizations across more than 20 countries, according to Arctic Wolf.
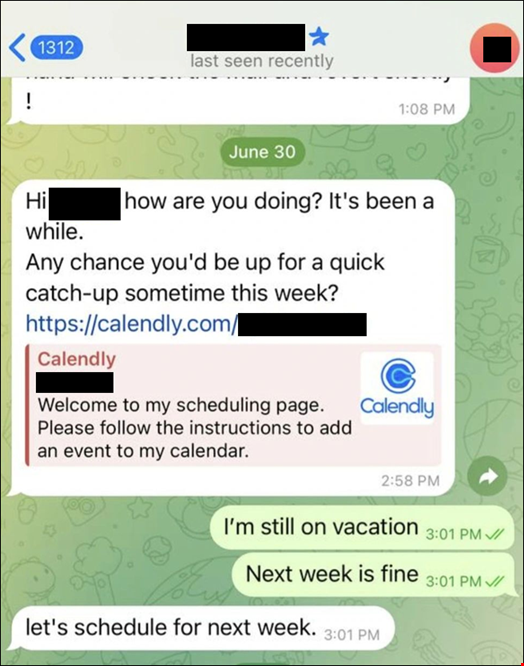
The spear-phishing campaign involved multiple social engineering techniques, including impersonating prominent figures of the fintech industry, typosquatted Zoom and Microsoft Teams meeting links, fake Calendly calendar invites and ClickFix-style clipboard injection attacks.
Arctic Wolf Labs researchers, who shared a detailed analysis of the full attack lifecycle in a report published on April 27, attributed the campaign “with high confidence” to BlueNoroff, a hacking team tied to the North Korea-linked Lazarus Group.
Spear-Phishing Via Typosquatted Links and Fake Meeting Invites
Arctic Wolf Labs first detected an intrusion by the attackers at a North American cryptocurrency company, beginning January 23, 2026.
The victim’s internal telemetry revealed a multi-stage execution chain initiated through a typosquatted Zoom meeting link delivered via a manipulated Calendly calendar invite.
When clicking the link, the victim was presented with a fake Zoom meeting interface that covertly exfiltrated their live camera feed to use as a lure in future attacks, while simultaneously deploying a ClickFix-style clipboard injection attack.
“A multi-stage credential extraction pipeline then plundered info from the victim’s device and browsers, focusing on cryptocurrency wallet extensions,” noted Arctic Wolf.
The initial attack commenced approximately five months after first contact with the primary victim.
However, the researchers noted that the execution chain itself swiftly progressed from initial click during a fake meeting to full system compromise in under five minutes. The threat actor reportedly kept access to the targeted systems for 66 days.
A Spear-Phishing Campaign Spanning Over 20 Countries
When Arctic Wolf Labs researchers further analyzed the infrastructure supporting this operation and the trail left by the threat actor, they identified 100 additional targets whose compromised media was hosted on attacker infrastructure.
The geographic distribution of victims is spread across over 20 countries and five regions, with the heaviest concentration in the US (41%), followed by Singapore (11%) and the UK (7%).
A large proportion of the targets (80%) worked in crypto, blockchain finance or adjacent sectors, with 45% being CEOs or founders.
The researchers also observed over 80 typosquatted Zoom and Microsoft Teams domains (registered between late 2025 and March 2026) on the same infrastructure.
The threat group’s media server also hosted over 950 files, revealing “a self-sustaining deepfake pipeline,” in which exfiltrated victim webcam footage was merged with AI-generated images to create fake meeting content, said the Arctic Wolf report.
The researchers found evidence of a PowerShell-based command-and-control (C2) implant, an AES-encrypted browser injection payload and a Telegram Bot API screenshot exfiltration mechanism.
BlueNoroff, The Group Behind Lazarus’ Bangladesh Bank Heist
Some tools and parts of the infrastructure used in this campaign are consistent with that of a known fake conference campaign publicly attributed to BlueNoroff by Kaspersky and Huntress.
According to Arctic Wolf, BlueNoroff is a subgroup of the Lazarus Group and is known under many aliases, including APT38, Sapphire Sleet, TA444, Stardust Chollima, CageyChameleon and Nickel Gladstone.
In a January 2026 report by Picus Security, BlueNoroff is described as “the financial cybercrime arm of Lazarus,” which has itself been publicly attributed to the North Korea’s Reconnaissance General Bureau (RGB).
Arctic Wolf stated that BlueNoroff has been active since at least 2014 and is focused on revenue generation through theft of cryptocurrency and financial assets.
The group first gained notoriety via the 2016 Bangladesh Bank Swift heist, in which the group attempted to steal $951m, successfully transferring $81m.
“The group has since pivoted toward targeting the cryptocurrency and web3 ecosystem through its long-running SnatchCrypto operation, which has been active since at least 2017,” added Arctic Wolf Labs researchers.
