Several civil society figures in Middle Eastern countries, including three high-profile journalists in Egypt and Lebanon, have been targeted by a spear-phishing campaign likely tied to a known South Asian cyber espionage group.
The campaign was detected by digital civil rights organization Access Now through its Digital Security Helpline in August 2025, following outreach from prominent Egyptian journalists Mostafa Al‑A’sar and Ahmed Eltantawy.
Access Now, a global non-profit organization, found that both individuals, prominent critics of the Egyptian government who have previously faced political imprisonment, had been targeted by spear-phishing campaigns carried out from 2023 to 2024.
Upon investigating the campaigns, Access Now discovered Android malware tied to the phishing infrastructure.
The NGO contacted researchers from mobile security firm Lookout, who assessed that the campaigns were “most likely” a hack-for-hire operation with ties to the Bitter advanced persistent threat (APT) group.
Bitter, also known as T-APT-17 and APT-C-08, is a suspected South Asian cyber espionage threat group that has been active since at least 2013. According to MITRE ATT&CK, the group has targeted government, energy and engineering organizations in Pakistan, China, Bangladesh and Saudi Arabia.
Researchers from ESET shared a report in October 2025 about two Android spyware strains posing as messaging apps and targeted users in the United Arab Emirates (UAE).
Lookout determined that these implants – dubbed ProSpy and ToSpy by ESET but only tracked as ProSpy by Lookout – were used in the targeting of civil society in the campaign identified by Access Now.
In parallel, SMEX, a Beirut-based non-profit organization advocating for digital rights across West Asia and North Africa, identified an unnamed high profile Lebanese journalist targeted by the same spear-phishing campaign in 2025.
New Spear-Phishing Campaign in the Middle East
According to an Access Now report published on April 8, attackers launched a spear-phishing campaign seeking to compromise Al-A’sar and Eltantawy’s Apple and Google accounts in October 2023 and continued in January 2024.
The NGO said the attackers “invested time and effort to establish a connection with the targets through various channels.”
To do this, they impersonated legitimate people and services using fake accounts and profiles, messages and pages to impersonate people and mimic common services and platforms to deliver the ProSpy/ToSpy malware.
The messaging app Signal was among the targeted platforms for the spear-phishing campaign.

In March 2026, Signal shared a public warning about such impersonation phishing campaigns.
Thinking he was receiving a legitimate message from Apple, Al-A’sar entered his account credentials, but refrained from engaging any further when he received a suspicious two-factor authentication (2FA) login notification from a distant location in Egypt.
Eltantawy did not engage at all with the phishing lures and the attackers ultimately failed in compromising his or Al-A’sar’s accounts, Access Now noted.
“If they had been successful, they would have gained unimpeded access to the personal and professional information in the targets’ Apple and/or Google accounts, including information on their families, associates and journalistic sources,” the researchers said.
This Android spyware could have allowed the attackers to access and extract victims’ files, personal contacts, text messages and geolocation, enable device microphones and cameras as well as instal further malicious apps on the target’s device.
The attack targeting the Lebanese journalist, documented by SMEX in a separate report published on April 8, used similar tactics, but was successful in compromising the target’s Apple account in 2025.
The campaign began in May 2025, with an initial attack delivered via Apple Messages. Two days later, a second wave followed through WhatsApp consisting of two separate phishing messages.
Both waves used the same malicious infrastructure and aimed to compromise the victim’s Apple Account.
After detecting the attacks, the target contacted SMEX’s Digital Forensics Lab (DFL) on May 25, prompting an immediate investigation due to the high risk and persistent threat.
While the first attack succeeded in breaching the Apple Account and adding a virtual device, forensic evidence was limited because the case was only reported days after the incident. The second wave failed, but researchers captured a complete credential exfiltration, including the username, password and 2FA codes, revealing that the same infrastructure was used in all attacks.
The analysis further showed that the attackers executed account takeovers in as little as 30 seconds from the moment the victim submitted their password.
Lookout researchers said they believe the same campaign also likely targeted victims in Bahrain, including Bahraini government entities, the UAE, Saudi Arabia, the UK, Egyptian government entities, and potentially the US or alumni of US universities.
Analysis of ProSpy Spyware
Lookout researchers also shared details about the ProSpy Android malware used in the campaigns, of which they acquired 11 samples, the earliest found in August 2024.
According to the researchers, while ProSpy is not as sophisticated as top-tier spyware like DarkSword, Coruna and Predator, it was developed “in a relatively professional way” using the Kotlin programming language. ProSpy integrates common spyware functions like collecting private information and exfiltrating sensitive files.
The sample analysis showed that its maintainers have added new capabilities over the years, indicating the spyware is actively being developed.
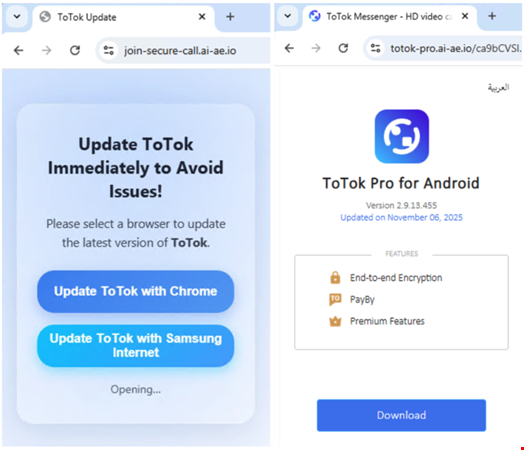
Lookout researchers also discovered live staging servers that are used to distribute ProSpy samples. These staging sites are simple, single page websites for specific messaging applications to lure victims to download the malicious APK files.
Typically, the threat group uses a two-stage attack to deliver ProSpy, first contacting targets via fake social media profiles or impersonating Apple Support, then tricking them into clicking spear-phishing links.
Apple users are lured with fake iCloud or E2EE app phishing pages, while Android users are directed to download ProSpy malware, such as through a fake ToTok app update hosted on deceptive domains like totok-pro[.]ai-ae[.]io.
The malicious site delivers an APK file in English and Arabic, disguising the attack with randomized URLs to evade detection.
Attribution to Bitter APT: Technical Links and Shifting Targets
Lookout researchers linked the ProSpy malware campaign to the Bitter APT group through multiple technical and operational overlaps.
They found shared infrastructure, such as the domain com-ae[.]net, previously tied to Bitter’s Dracarys malware, along with code similarities, including worker-class naming conventions, numbered command-and-control (C2) commands and the use of "pro/premium" lures in app titles.
While ProSpy and Dracarys were developed years apart, the structural and behavioral parallels, combined with Bitter’s history of targeting Android devices and using PHP-based C2 infrastructure, strengthened the attribution.
However, Lookout noted that Bitter’s typical targets (military, energy and government entities) didn’t align with the civil society and opposition figures compromised in the ProSpy campaign identified by Access Now and SMEX.
This discrepancy, along with past overlaps between Bitter and Indian hack-for-hire groups led researchers to conclude that the operation may represent either an expansion of Bitter’s scope or a collaboration with a hack-for-hire outfit tied to South Asia.
While no direct links to known mercenary groups were found, evidence suggested Bitter, or a closely affiliated entity, was likely hired to conduct espionage in the Middle East and North Africa region, marking the first documented case of the group targeting civil society.
