Russian hacking group APT28 has been exploiting vulnerable internet routers to redirect traffic through attacker-controlled servers and steal credentials from targeted organizations, the UK government has warned.
In a new advisory published on April 7, the UK’s National Cyber Security Centre (NCSC) said it detected two new malicious campaigns it attributed to APT28.
Both campaigns are linked to a list of virtual private servers (VPS), which have been actively modified by APT28 since 2024 to operate as malicious domain name system (DNS) servers.
“These VPSs typically receive high volumes of DNS requests originating from routers that had been exploited by the actor likely utilising public vulnerabilities,” the NCSC advisory noted.
The NCSC assessed that the initial DNS hijacking operations are “opportunistic in nature,” meaning that the APT28 hackers likely use this method to first gain visibility of a large pool of candidates and then filter down users at each stage in the exploitation chain to triage for “victims of likely intelligence value.”
The UK government associates APT28 “almost certainly” to the Russian General Staff Main Intelligence Directorate’s (GRU) 85th Main Special Service Centre (GTsSS) Military Intelligence Unit 26165, is known under many other names, including Fancy Bear, Forest Blizzard, Strontium, the Sednit Gang, and Sofacy.
In a separate report, also published on April 7, Microsoft Threat Intelligence said APT28 and and its sub-group tracked as Storm-2754, started compromising VPS servers to exploit small office/home office (SOHO) routers "since at least August 2025."
First Activity Cluster Targets TP-Link Routers
In the first activity cluster identified by the British cybersecurity agency, the dynamic host configuration protocol (DHCP) DNS settings of compromised SOHO routers, mostly TP-Link routers, were modified to include actor-owned IP addresses.
One of the router models appearing in this campaign, the TP-Link WR841N, was likely exploited using CVE-2023-50224, a vulnerability that enables an unauthenticated attacker to obtain information such as password credentials via specially crafted HTTP GET requests.
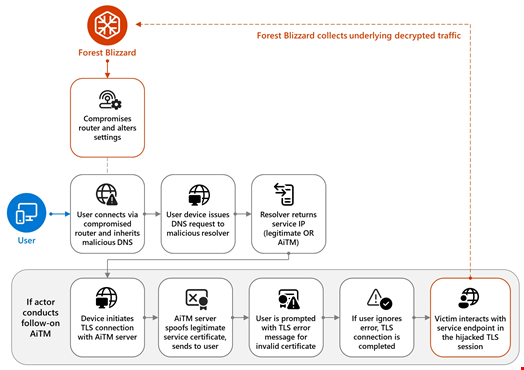
These settings were subsequently inherited by downstream devices, for example laptops and phones, leading requests matching APT28’s targeting criteria to be resolved by the malicious DNS servers to IP addresses owned by the threat actor.
The APT28 hackers would then attempt to conduct adversary-in-the-middle (AitM) attacks against follow-on connections, including user browser sessions and desktop applications, likely to harvest passwords, OAuth tokens and other credentials for web and email related services.
“Subsequent malicious logins using this stolen data may originate from further infrastructure not listed in this advisory,” the UK agency noted.
Read more: US – FCC Bans Foreign-Made Routers Over National Security Concerns
Second Activity Cluster Targets MikroTik and TP-Link Routers
In a second activity cluster, the NCSC observed a subset of servers receiving DNS requests via likely compromised devices including models of MikroTik and TP-Link routers.
In this campaign, the DNS requests were forwarded from these servers to further remote actor-owned servers.
This cluster of infrastructure was also involved in interactive operations against a small number of MikroTik routers, often located in Ukraine, that were likely of intelligence value to the actor.
NCSC Recommendations to Stop APT28’s Credential Theft
The NCSC provided a list of mitigation measures that could help in defending against the activity described in the advisory. These include:
- Using browse-down architecture to prevent attackers easily gaining privileged access to your most vital assets
- Using the latest supported versions, applying security updates promptly, deploying antivirus and regularly scanning to detect known malware threats
- Adding applications to an allowlist
- Deploying a host-based intrusion detection system
- Using multifactor authentication (MFA)
The NCSC has previously attributed activity to APT28, including the 2015 cyber-attacks against the German parliament and an attempted attack against the Organisation for the Prohibition of Chemical Weapons (OPCW) in April 2018.
