‘Cybersecurity’ is a term of the moment but, at its heart, does the idea of cybersecurity represent anything new? This is an especially poignant question for those who have been in the cybersecurity business for a number of years.
This is a question that we have been wrestling with during the monthly meetings of Royal Holloway’s “Cyber Security Club”, which is an industrial research forum comprising representatives of government, industry and academia. The club operates under the ‘Chatham House Rule’ and benefits from Royal Holloway providing a neutral venue where members can share ideas in a relaxed and stimulating environment. The consensus emerging from the club is that the answer to the opening question is “no... and yes...”.
At its heart, we believe that cybersecurity is not so fundamentally different from much of what has gone on before. The ‘security’ element has not significantly changed from days when ‘information security’ was a more popular term. After all, much of cybersecurity involves the provision of security services such as confidentiality, integrity, availability, and increasingly exotic variants.
What then are we to make of the ‘cyber’ part of this description? The term cyber has come to represent the transformed landscape of services and applications that we now live in. In the last twenty years we have seen many significant changes: connectivity has massively increased; the variety of services, users and devices comprising the internet has dramatically expanded; and the sophistication and mobility of technology is far greater than before. Yet, we believe that the basic security service framework within which all of this cyber activity operates has not changed over the last generation.
So is anything different about cybersecurity?
One key aspect that we believe has made a big difference is the accelerating pace of change. This is happening at several different levels.
The technological changes are one thing, but perhaps more significant are the changes to the way business is engaging with technology and, perhaps even more significant, the new ways in which society is engaging with technology. The rise of social networking and its wider implications on, for example, the political landscape, mean that in some areas governments and businesses are finding it increasingly difficult to influence what is happening. As a result, it seems to be progressively harder to provide traditional notions of security.
Another difference is the ever-increasing level of interconnectivity, which is having a number of effects that we do not yet fully understand. For one thing, it is increasingly difficult to isolate roles and responsibilities. Another impact is that major events have the potential to dramatically change the threat landscape. Both of these factors make the impact of failure harder to assess, which in turn makes it challenging to conduct risk management.
So, what needs to be done to move things forward?
Although not a new suggestion, we firmly believe that now – more than ever before – there is a need for improved interaction between business and security units to address the fundamental challenges. One of these is that the risks in cyberspace are hard to judge and analyze; indeed, in many cases, experts disagree about the severity and scale of threats in cyberspace.
We also struggle to make balanced trade-offs between risks and benefits, in part because we don’t have the right language within which to frame their analysis. This is not helped by the fact that we currently have a limited understanding of the ways that human nature influences risk appetite in a cyber-context.
Over the last few decades, information security experts have developed a toolkit of techniques for addressing some of the problems that we now encounter in cyberspace. Many of these may still be suitable in certain contexts. However, there is definitely a need for some new approaches, as well as urgency to understand the limitations of the tools that we already have. The provisioning of ‘cybersecurity’ requires that we develop new tools, potentially by looking at other fields – such as psychology, sociology, criminology, economics – in the search of alternative, sympathetic controls in addition to those we already have.
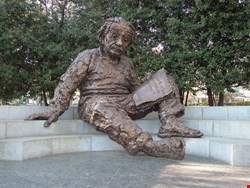
The environment we call cyberspace is in a state of dynamic change, and we must not expect different results by trying the same old things which, as Einstein famously stated, is a route to insanity. In this respect, above all others, cybersecurity is something new.
| Royal Holloway, University of London is exhibiting at Infosecurity Europe 2013, the No. 1 industry event in Europe held April 23–25, 2013, at Earl’s Court, London. The event provides an unrivaled free education program, exhibitors showcasing new and emerging technologies and offers practical and professional expertise. Visit the Infosecurity Europe website for further information. |
Dr Geraint Price is a Lecturer in Information Security at Royal Holloway, University of London. Keith Martin is a Professor of Information Security at Royal Holloway, University of London.